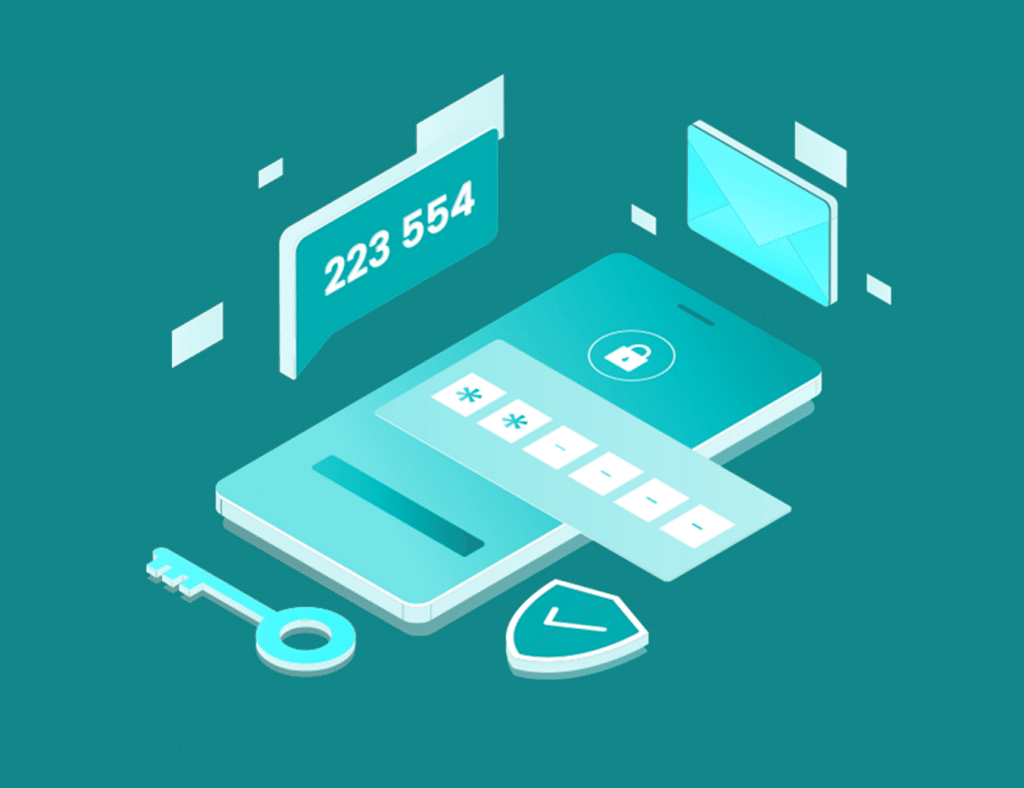
Protect your sensitive banking resources with Silverfort’s MFA solution.
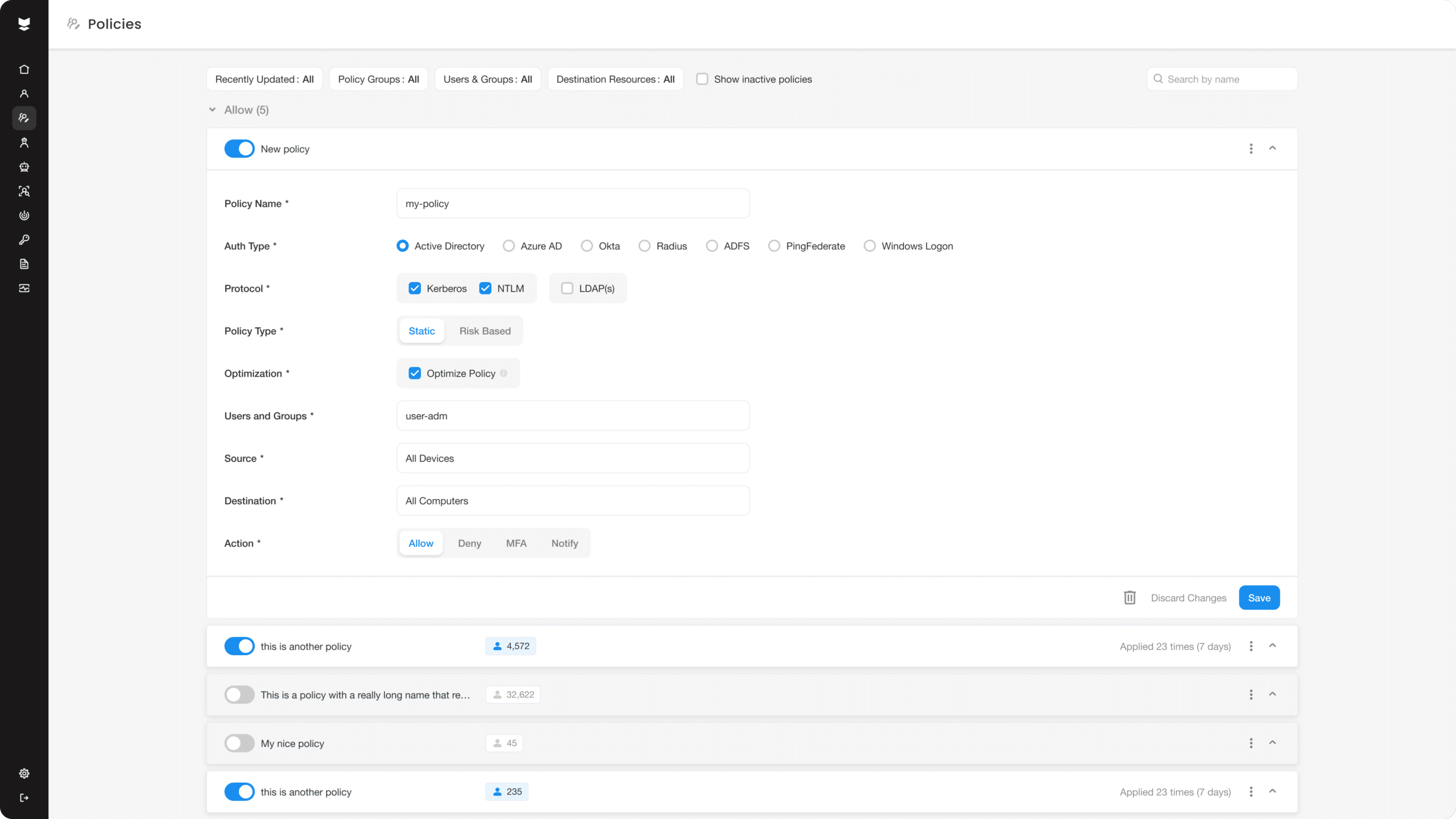
Silverfort enables banking firms to implement secures access to their banking infrastructure with unprecedented accuracy and efficiency. Our solution takes care of all your MFA needs – from device-based authentication to biometric authentication. With Silverfort, you can provide your customers with a seamless and secure banking experience, while safeguarding their personal and financial information from cyber attackers. Get in touch with us today to learn more!