The surge in ransomware attacks has led leading underwriters to raise the bar for renewal or purchase of cyber insurance policies. Customers are now required to deploy various security measures – such as Multi-Factor Authentication (MFA). As a result, cyber insurance brokers – the ones that actually sell the policies– are tasked with finding an MFA solution that can both satisfy underwriters’ requirements as well as be easily adopted by their customers. However, this is not as easy task as one might think.
This article provides brokers with a definitive list of questions they should ask themselves when choosing the MFA solution they’ll recommend to their customers. If the answer to all of them is ‘Yes’, the solution is good to go.
Are you a broker reading this article? If so, let’s start!
The Cyber Insurance MFA Companion to Choosing the Right Solution
If you’re a broker and you want to sell cyber insurance policies, you must make sure that MFA is deployed in the customer’s environment. And the best way to do that is to have an MFA solution that you can recommend them.
In theory all you need to do is to randomly choose one of the multiple MFA solutions in the market. In practice, however, it’s not that easy because not all MFA solutions are equal. In fact, it’s extremely important for you to choose the right MFA solution. A wrong MFA solution, for example, might be too hard to deploy in your customer’s environment, or won’t be able to provide adequate protection.
The wrong MFA solution can harm you in two ways. The more straightforward way is by not satisfying your underwriter’s security requirements – making the customer ineligible for a policy. The other – and possibly worse for you – is that you’ll succeed in selling the policy, but your customer will fall victim to a ransomware attack, resulting in a policy claim for which your underwriter will hold you accountable.
So how can you single out the best-fit MFA solution for your customers? Here are the top 5 considerations you should bear in mind when choosing your MFA.
# 1 Can the MFA solution be deployed seamlessly and rapidly?
This might come to you as a surprise, but the most important feature of security products is their ease of use, starting from the initial deployment. The rule of thumb is that everything that takes more than a week to get started will end up not implemented at all. So first and foremost, check whether the MFA vendor can vouch for a fast and sleek deployment process. If the answer is positive, you can proceed to the next item.
#2 Does the MFA solution cover the internal environment?
This is a classic ‘fine print’ catch. The underwriter says the customer must have ‘MFA’. Now, all MFA solutions without exceptions can be used for remote connection to the customer environment. However, that’s not all your underwriter wants. If you take a closer look into the assessment’s form tables and checklists, you’ll discover that significant attention is given to connections that take place within the internal environment itself. Not all MFA solutions support this. So, make sure that the one you’re evaluating as a recommendation to your customers applies to internal environment use cases- for example, a user that access a file server from his/her computer, or opens a file on a shared network folder.
#3 Can your customer apply the MFA solution to privileged users’ access?
Your underwriter’s goal by requiring MFA is to reduce the likelihood of a successful ransomware attack. Ransomware threat actors would typically strive to compromise the accounts of your privileged users, since this will easily pave their way to any resource in the targeted environment. As a result – and that’s more fine print you should consider- your underwriter is especially concerned about the protection of your customers’ privileged users and the ability to easily discover who these users are and apply MFA protection to them. The solution you choose must be able to support that.
#4 Is the MFA solution capable of protecting command-line access?
This question relates again to the underlying root cause for which underwriters had started to require MFA in the first place – to nullify attackers’ ability to utilize compromised user credentials to access resources in your customers’ environment. It’s important for you to know that there are multiple ways in which this access can be carried out. Some are trivial to protect with MFA, such as Remote Desktop Protocol (RDP), but others are beyond the scope of most commercial MFA solutions, like command-line based tools such as PowerShell and PsExec. Not surprisingly, these are the access methods threat actors prefer to employ, so your MFA solution of choice must be able to cover them as well.
#5 Can you enforce it on 100% of authentications and access attempts?
When sailing a boat, a single crack in its hull can sink it even if the rest of it is whole and intact. Your customers are required to have MFA across 100% of their assets. Anything less than that means a likely breach. The MFA solution you should pursue must have the ability to vouch for complete coverage to satisfy your underwriter’s requirements, and the ability to reach this coverage in a rapid and easy manner.
Silverfort MFA – One Solution for all Cyber Insurance Requirements
Silverfort has pioneered the first Unified Identity Protection platform that can enforce MFA protection across all users, systems, and environments. Silverfort MFA has been embraced by top underwriters and hundreds of customers that sought to renew their existing cyber policies or purchase new ones.
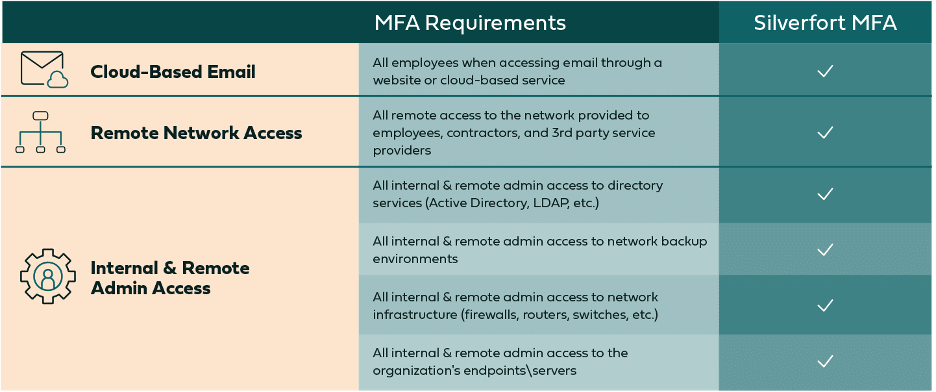
The following table shows how Silverfort addresses all the key capabilities underwriters require:
Offering Silverfort to your customers is the safest and most rapid path to add another customer’s cyber policy purchase to your portfolio.
Visit our website to learn more about Silverfort’s MFA protection for cyber insurance or download this eBook to learn more.

