By Yaron Kassner, CTO and Co Founder, Silverfort
On May 14th, 2019 Microsoft issued a patch against the so-called BlueKeep vulnerability, which is also known as CVE-2019-0708. The patch fixes a critical Remote Code Execution vulnerability. According to Microsoft: “This vulnerability is pre-authentication and requires no user interaction. In other words, the vulnerability is ‘wormable’, meaning that any future malware that exploits this vulnerability could propagate from vulnerable computer to vulnerable computer in a similar way as the WannaCry malware spread across the globe in 2017.”
1 Microsoft TechNet announcement about the patch for fixing CVE-2019-0708
Microsoft was quick to release the patch and is putting major efforts in to making sure their customers patch their systems. The severity of this vulnerability drove Microsoft to take the unusual step of issuing patches not only for current affected systems like Windows 10, Windows 7, Windows Server 2016, and Windows Server 2008 R2, but also for systems that are no longer supported like Windows 2003, Windows XP, and Windows Vista. Microsoft security officials say they are confident BlueKeep exploits already exist and may have the potential to trigger self-replicating attacks as destructive as the 2017 WannaCry attack that shut down computers all over the world.
The BlueKeep vulnerability should be taken very seriously. This vulnerability can be exploited to achieve an initial foothold in a network by attacking internet exposed remote desktop servers, and it can also be used by attackers to move laterally in the network after obtaining this initial foothold.
While applying this patch is of paramount importance, patching all servers in an organization can be a very difficult tasks for enterprises. It’s important to remember that even a single unpatched endpoint can enable a breach. Evidently, the EternalBlue vulnerability was exploited on a massive scale well after the patch was released by Microsoft.
Partial exploits have already been released for the BlueKeep vulnerability, so it is just a matter of time before the vulnerability is widely used by attackers.
Protecting Your Systems from the BlueKeep vulnerability:
The first thing you should do is identify any unpatched or old operating systems in your network and patch all affected systems – this should be done as soon as possible!
Next, you should use Network Level Authentication (NLA) where possible: NLA requires authentication before the vulnerability can be triggered. Microsoft strongly recommends this, yet it isn’t the default setting.
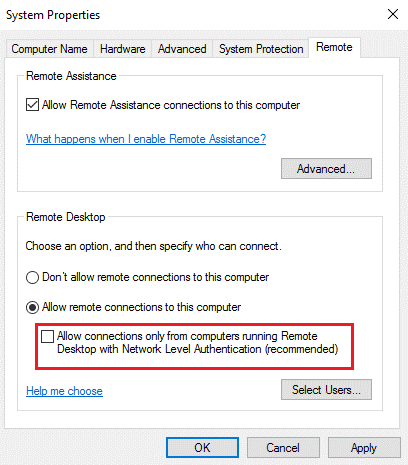
2 Enabling NLA to require authentication before the vulnerability can be triggered
Enabling NLA prevents pre-authentication execution. However, it’s important to remember that affected systems are still vulnerable to Remote Code Execution (RCE) exploitation if the attacker has valid credentials that can be used to successfully authenticate.
Preventing Exploitation of Compromised Credentials for Remote Code Execution with Silverfort
As mentioned above, enabling NLA is critical for preventing the pre-authentication execution, but it’s not enough because if an attacker already has valid credentials (which are quite easy to get these days), the attacker and still gain access and exploit the RCE vulnerability. This is where Silverfort comes in and prevents the use of compromised credentials for RCE exploitation and other remote desktop protocol attacks:
Silverfort’s agentless, proxyless authentication platform can enforce multi-factor authentication (MFA) and strong authentication policies to prevent unauthorized access to any system, no matter what it is or where it is – whether on-premises or in the cloud. This includes systems that couldn’t be protected by MFA solutions until today, like IT infrastructure, homegrown and legacy applications, file shares, databases, and more.
When an attacker tries to exploit compromised credentials to gain access to a system, Silverfort can require a second authentication factor to validate the user’s identity. While legitimate users can easily authenticate, an attacker will fail the 2nd authentication factor and therefore his/her access will be denied.
Silverfort can apply static MFA policies that require users to authenticate with a 2nd factor any time they access systems, but that can be quite disruptive. Therefore, risk-based adaptive policies are highly recommended: Adaptive policies can be set to require a 2nd authentication factor only when risk levels are high – this helps minimize disruptions without compromising security.
To read more about Silverfort’s adaptive policies and AI-based Risk Engine download this free whitepaper.
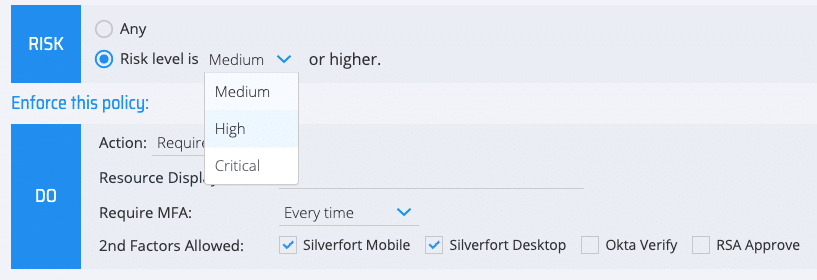
3 Silverfort can apply static MFA policies or risk-based adaptive authentication policies
Stopping Lateral Movement with Zero-Trust Security Policies
Silverfort can enforce MFA and secure access not only for external access, but also inside corporate networks. This includes both user-to-machine access and machine-to-machine access (service accounts).
Service accounts are used by various corporate systems to communicate with other systems and automate processes. Such accounts are a prime target for attackers, since they are often equipped with high privileges and their passwords are rarely changed. But because these accounts are used by machines, rather than humans, they cannot be protected with regular multi-factor authentication methods.
Silverfort introduces a unique capability for securing the use of service accounts, which prevents unauthorized entities from stealing or misusing them. This is achieved without any change to the relevant systems.
Silverfort enables organizations to implement a holistic zero-trust security model without deploying software agents or proxies, and without requiring changes to existing networks. Its innovative architecture ensures secure access to any system, no matter where it is, or what it is. This includes user-to-machine and machine-to-machine access, as well as any administrative access. Because Silverfort avoids any modifications to existing assets and infrastructure, it allows not only small agile companies but also large traditional enterprises to achieve zero trust security throughout their networks.
Yaron Kassner, CTO and Co Founder, Silverfort
Silverfort’s CTO and Co-Founder Yaron Kassner is a cybersecurity and big data technology expert. Before co-founding Silverfort, Yaron served as a big data expert consultant for Cisco. He also developed new capabilities involving big data analytics and machine learning algorithms at Microsoft. Prior to that Yaron served at the 8200 elite cyber unit of the Israel Defense Forces, where he led a reputable R&D team, raised to the rank of Captain, and received a prestigious excellence award. Yaron holds a B.Sc. in Mathematics, Summa Cum Laude, an M.Sc. and Ph.D. in Computer Science from the Technion – Israel Institute of Technology.
Want to learn more or see a demo? – Contact us today!

