As recently reported, Okta recently experienced a security breach where the source code for its workforce identity cloud was stolen. As Silverfort partners with Okta, to protect our joint customers’ workforce identities we want to share with you our insights regarding this attack and subsequent precautionary steps organizations should take to strengthen their protection from the potential risk this introduces.
No Immediate Risk Detected
First, it’s important to note that there is no immediate impact to any Okta customers, as Okta has found no unauthorized access to its service or customer data.
Okta has taken the correct, responsible measures in response to this breach, including reviewing and fortifying their GitHub security as well notifying their customers.
Immediate Concerns and Long-Term Implications
There are, however, potential immediate and long-term implications of this breach. While Okta does not rely on the secrecy of their source code for the security of its services, its leak would enable adversaries to research it for vulnerabilities in a much easier manner — it’s highly likely that threat actors are engaged in this type of research right now, already planning the next steps of the attack.
Additionally, considering this is one of several Okta breaches this year, it’s likely that attackers are attempting to target Okta customers by compromising Okta’s service and infrastructure. Since Okta stores users’ passwords, this risk should be addressed.
Okta Breach Potentially Exposes the Active Directory Environment to Malicious Access
Therefore, Silverfort recommends a zero-trust approach to protect identities in Okta.
The most effective solution against compromised passwords is multi-factor authentication (MFA). While Okta provides MFA to SaaS and web applications of its customers, it does not support the Active Directory (AD) environment with similar protection. Since passwords stored in Okta are usually synced with Active Directory, this lack of MFA creates a critical exposure to malicious access via compromised credentials.
Silverfort and Okta Integration Protects the Active Directory Environment
The integration between Silverfort and Okta enables Okta users to extend MFA protection to the entire Active Directory environment, creating an additional protection layer to mitigate possible adversary actions following the Okta breach.
Use Silverfort Free Identity Threat Monitoring to Increase Resilience
Silverfort offers a free 60-day identity threat monitoring package for Okta customers that have their Active Directory and Okta users synced. You can activate this free offering here.
With Silverfort, you can perform the following mitigation steps:
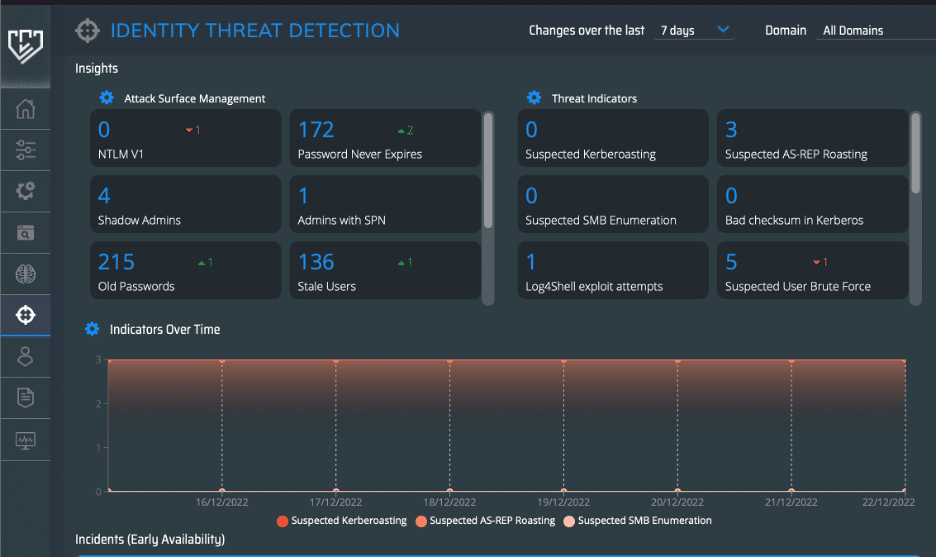
Continuous Monitoring
- Attack Surface Management: Monitor any AD authenticated system, legacy app, command line interface (CLI), or OT system that may have synced passwords with Okta.
- Active Attacks: Monitor for detected identity threats and leverage Silverfort’s identity data for a rapid and efficient response.
Active MFA Protection
- GitHub will require MFA by the end of 2023, if not sooner. Enable MFA using Okta for all SaaS apps.
- Extend your MFA solution to all on-prem AD authenticated apps.
Utilizing the Silverfort–Okta integration provides a rapid and safe way to keep your environment secure against any potential identity threats that will result from this breach.

