Strengthen Your On-Premise AD with Stronger MFA Security—Powered by Silverfort.
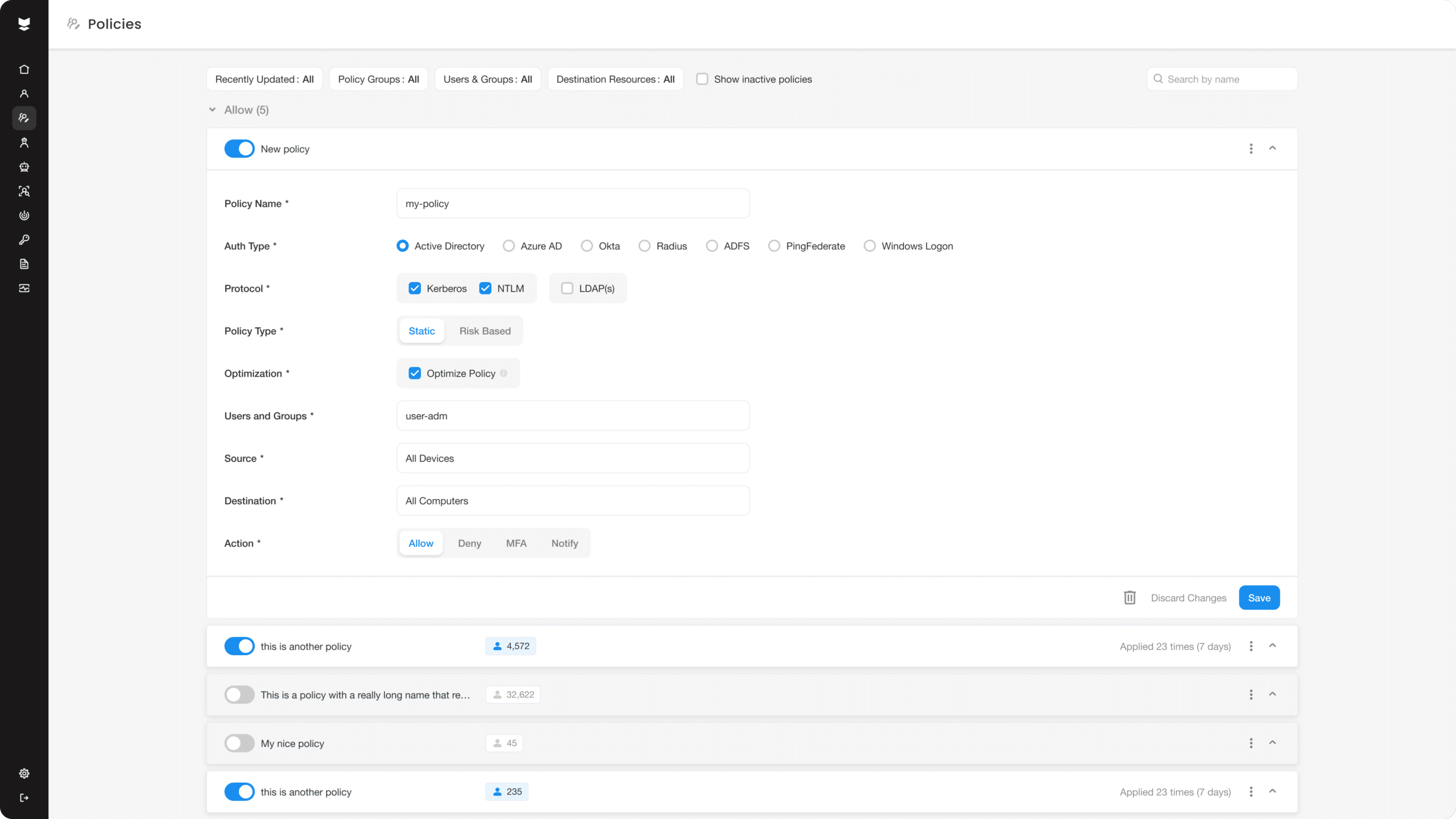
Silverfort is the ideal solution for MFA for On-Premise Active Directory. With its innovative platform, Silverfort removes the need for user interaction during the authentication process, providing complete protection against account takeover and unauthorized access. The AI-driven solution seamlessly integrates with your existing security infrastructure, so that you can easily implement On-prem MFA for Active Directory without any disruption.