Identity is now the #1 attack surface
24B
compromised credentials are offered for sale in the dark web.
97%
of enterprises rely onrnlegacy or hybrid IAM infrastructure.
82%
of data breaches and ransomware attacks involve compromised credentials.
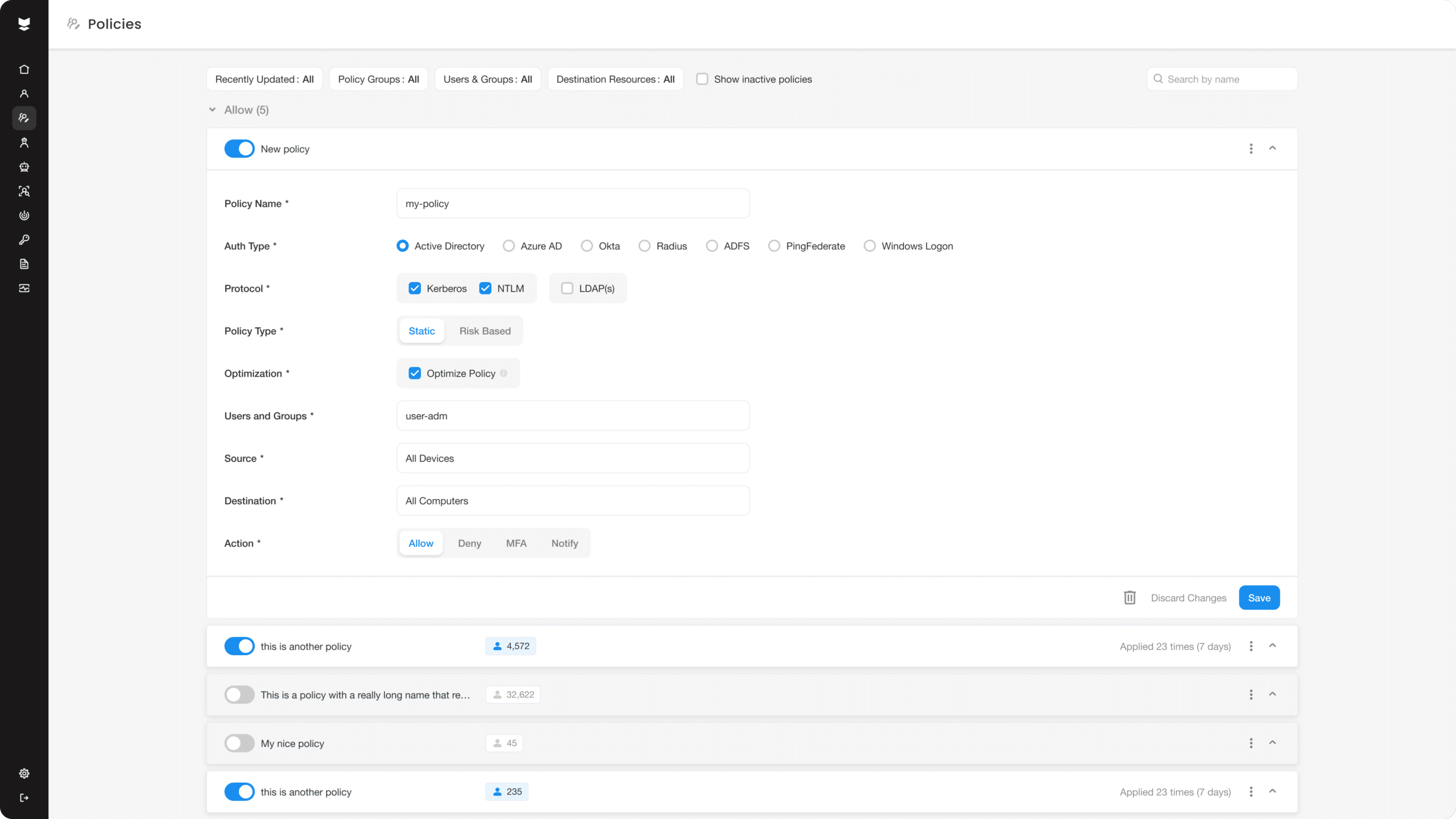
Protect all your resources and access interfaces
Replace your traditional MFA solution
Silverfort’s MFA solution for Azure offers adaptive risk-based authentication, improving security without compromising user convenience or productivity.
Add MFA protection
Helps fortify Azure security by seamlessly integrating with legacy systems and providing adaptive risk-based authentication.
Extend your MFA solution
Silverfort’s MFA solution provides secure and agentless MFA for Azure, benefiting previously unprotected environments.
Trusted by 1,000+ organizations.
Identity security is the heart of our mission. We build true partnerships with our customers to achieve it together.
The results speak for themselves.
Trusted by 1,000+ organizations.
Identity security is the heart of our mission. We build true partnerships with our customers to achieve it together.