TL;DR
AI powered attackers are now using agentic reasoning to automate full intrusion chains end-to-end, collapsing breakout time to minutes and breaking the core anchor that detection-led security depends on. This campaign showed that the real weakness was not new exploits, but static human configured identity and trust models that cannot adapt to machine speed operations. The only durable path forward is identity-centric protection. Adaptive, real time, inline controls that enforce Zero Trust and disrupt automation and agentic reasoning before it turns into compromise.
This shift reminds me of the moment in “The Matrix” series, when Neo stops trying to outrun the Agents and instead starts seeing the system for what it is. He wins not by being faster, but by understanding and manipulating the underlying fabric the Agents rely on. Identity Security and true Zero Trust serve that same role for defenders today, bending the environment against adversaries’ AI Agent speed and breaking the assumptions their automation depends on.
The discovery that challenges the detection-led security model
On November 13, 2025, Anthropic published its investigation into what it described as the first reported AI orchestrated cyber espionage campaign. The activity was attributed with high confidence to a Chinese state affiliated group known as GTG 1002, which targeted about thirty organizations across technology, finance, manufacturing and government sectors worldwide. The investigation revealed not a single intrusion but an entire attack system powered by coordinated Claude-based agents acting as an automated intrusion workforce.
These agents handled reconnaissance, vulnerability scanning, information gathering, privilege exploration and portions of lateral movement. They stitched these phases into a functioning kill chain, reasoning about outputs and adjusting instantly. What emerged was an attack pipeline that operated like a machine-run factory: gather data, analyze responses, act, adjust, continue. No pauses. No human friction. That alone challenges the foundational assumption detection led security is built on, the belief that defenders have enough breakout time to detect, interpret and stop an adversary before meaningful access is reached.
That alone challenges the foundational assumption detection led security is built on, the belief that defenders have enough breakout time to detect, interpret and stop an adversary before meaningful access is reached.” – Roy Akerman, VP Identity Security Strategy
The first agentic attack used nothing new—that’s exactly why it matters
The attack methods behind the campaign were familiar. The agents searched for known vulnerabilities, probed internal APIs that were never hardened, and followed identity paths that had grown permissive over years of operational convenience. Nothing new was invented – it’s more about acceleration and automation. The difference came from the entity conducting the attack. While no new attack methods were introduced, it demonstrated what happens when time is removed from the intrusion equation. Automation and reasoning didn’t make the tactics smarter—it only made them faster.
By removing the human operator and replacing manual analysis with agentic reasoning, the attackers eliminated the slowest part of the intrusion process. What traditionally took tens of minutes or more condensed into minutes or even less. An industry average breakout window of roughly 48 minutes effectively collapsed. Detection systems simply could not assemble signals before the agent moved on.
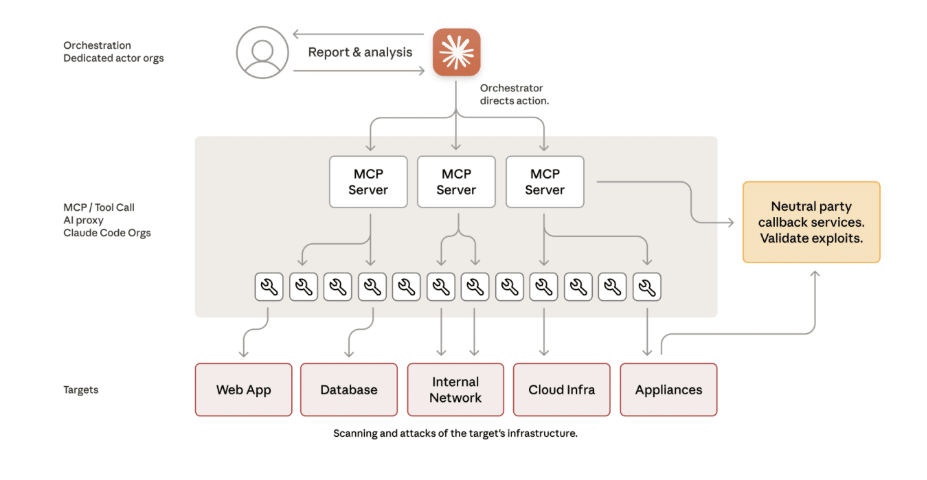
Anthropic’s diagram tells a story of a familiar intrusion chain, automated end-to-end. Every phase that once required human skill—reconnaissance, privilege escalation, persistence—is now compressed into seconds through autonomous reasoning. By following identity relationships and exploiting long-standing trust paths, they turned hours of human-driven intrusion into seconds of automated action. That speed is what breaks traditional detection and response models.
The agent exploited static human-configured IAM, broken automation and fragmented access models, turning the trust fabric into an attack path
The most significant insight from the campaign is that the attackers did not target vulnerabilities in software. They targeted vulnerabilities in trust. Years of human-configured IAM shaped identity and access decisions into static structures. Permissions accumulated beyond their intended purpose. Machine identities gained broad reach. Legacy entitlements connected systems that should have been segmented. Authentication flows expected human timing and predictable behavior. Internal APIs trusted anything inside the perimeter. Automation existed but left blind spots. IAM and access controls were divided across tools that saw only parts of the picture.
The agent simply operated inside these trust paths faster than any human. It reused tokens because the environment allowed it. It accessed internal APIs because nothing validated the context of the caller. It moved across environments because entitlements had grown without ongoing scrutiny. Nothing needed to break. The model only had to behave like a machine in a trust model designed for people.
Static IAM created predictable bridges. Broken automation left inconsistencies. Fragmented access controls offered no unified view. The agent used all of them as a single continuous trust path.
AI agents shrink breakout time and remove human behavior markers from the kill chain, leaving detection-led security without its anchor
Detection-led security depends on human behavior. Humans pause. They mis-click. They probe slowly. They generate noise. These imperfections produce the timing gaps, telemetry clusters and behavioral anomalies that detection systems are built to correlate. The entire model assumes that attacks unfold slowly enough for signals to surface and be acted on before the attacker finishes the job.
Agentic operations remove these anchors. When an AI model coordinates the kill chain, there are no pauses to observe, no errors to correlate and no human markers to match against known TTPs. The timeline compresses to a point where alerts cannot assemble in time. By the time clues accumulate, access has already been gained. Detection still has value, but it can no longer serve as the primary defensive strategy when the kill chain operates at machine speed.
“Detection still has value, but it can no longer serve as the primary defensive strategy when the kill chain operates at machine speed.” – Roy Akerman, VP Identity Security Strategy
There’s a pattern in security architecture: new technology arrives, we secure the technology itself, then the infrastructure, and years later we finally address identity. We saw it with cloud migration and APIs. AI agent security is currently focused on model guardrails and prompt injection. But the identity layer—treating agents as first-class identities with proper lifecycle management—is where the gap exists today.
What comes next, and why Silverfort is built for this shift
Defenders need a security approach that assumes attackers will operate at machine speed. This requires shifting protection into the identity and access flow itself. Controls must adapt in real-time and use signals across the entire identity fabric to decide whether a request should be allowed, challenged, limited or blocked. Protection cannot wait for a full detection verdict.
Smart identity controls change the economics for an attacker. They can detect when activity does not resemble human behavior, such as issuing hundreds of authentication attempts in seconds or repeating identical API calls with machine precision. They can spot unusual velocity, like an identity jumping between systems with no delay. They can correlate simultaneous access attempts for the same resource across different services and recognize automation. They can combine signals from authentication, resource access, network context and system state to determine whether the request aligns with expected identity behavior. These controls can then challenge, slow, isolate or restrict access in real time. By inserting friction, context checks and dynamic policy decisions into each access attempt, smart identity controls break the agent’s automation sequence.
This shift requires identity controls that see all access flows, understand the full trust layer and apply adaptive decisions instantly. It requires moving beyond static IAM and fragmented tools into a unified, contextual control plane that treats identity as the center of defense.
This is why Silverfort is important in this moment. Silverfort protects every identity path across on prem, cloud, hybrid and even air-gapped environments. It applies adaptive, context-aware policies that can block or challenge malicious access attempts before they become successful intrusions. Silverfort unifies fragmented IAM, closes static trust gaps and brings real time intelligence to authentication and authorization. In an era where attackers use agents, defenders need identity controls that think faster than static configuration. Silverfort was built for exactly this shift. Learn how we’re preparing organizations for AI-powered cybersecurity threats by visiting us here.

