Antrophic’s Mythos panicked the market, and after seeing what it does up close—running it against real enterprise environments alongside customers with access, and spending weeks in conversation with CISOs and IAM leaders who are actively rewriting strategy—I understand why.
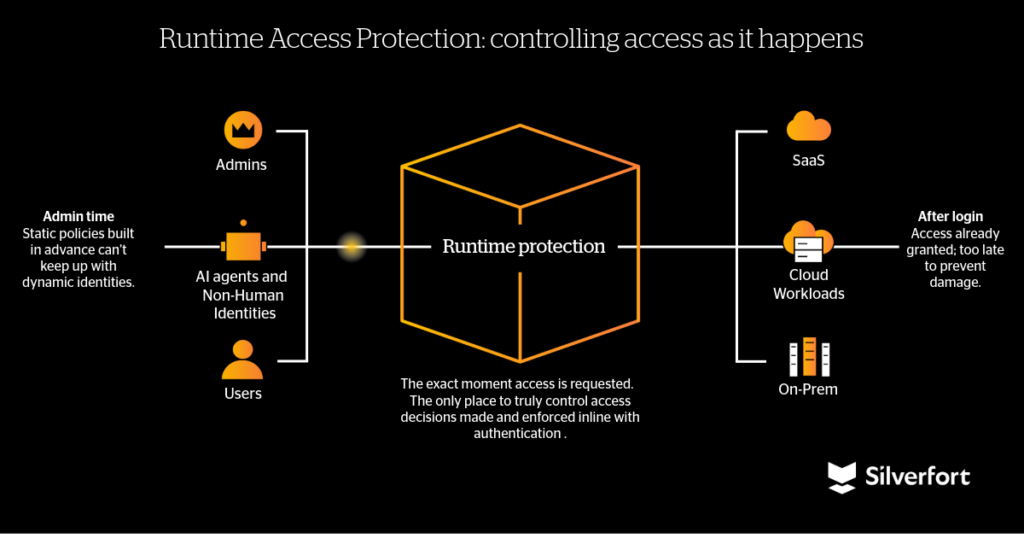
The core finding is not about novel techniques. It is about time. Mythos compresses the full attack chain into minutes, collapsing the assumptions that detection, governance, and vulnerability management have silently depended on for thirty years. What remains standing is runtime control: evaluate identity, understand context, assess risk, enforce access decisions inline, before authentication completes. That is what Silverfort was built from the ground up to deliver; first in Active Directory, then in the cloud, and now with AI agents.
What Mythos is and why it matters
Anthropic released Claude Mythos Preview in April 2025 as a deliberately-restricted model built for advanced cybersecurity tasks. In the weeks that followed, 38 independent researchers documented findings that went well beyond benchmarks: complex vulnerability chains identified overnight, working exploits produced with minimal human guidance, and autonomous offensive reasoning at a scale not seen before.
The Glasswing program took this into enterprise environments, where organizations ran Mythos against themselves in controlled red team scenarios. The pattern was consistent: standard attacker playbooks executing at a speed that left no realistic window for human response. This was not a surprise in isolation. Anthropic’s November 2025 report had already documented an AI-assisted espionage campaign where agentic capabilities moved beyond advisory roles and actively participated in intrusion execution. With AI-based simulated attack tools now broadly available, the trajectory is clear: these capabilities are no longer restricted to a single model or a controlled program.
The attack chain is now measured in minutes, and identity is the frontier
AI agents execute attacks at machine time. No hesitation, no prioritization. They enumerate identities, test credentials, chain misconfigurations, pivot, and exfiltrate in one continuous flow, across every viable path simultaneously. The data tells the story: in 2025, average breakout time dropped to 34 minutes. Fastest lateral movement: four minutes. Exfiltration in as little as six. Those numbers predate Mythos as the attacker.
The shift is not in technique. Reused credentials, ESC1 misconfigurations, over-privileged accounts—none of this is new. What is new is the economics: the cost of discovering and chaining these weaknesses has collapsed to near-zero. This is why identity and access disciplines are at a critical inflection point. Software gets patched. Networks get segmented. Endpoints get hardened. But every action, human, machine, or AI agent, has to authenticate. For IAM, PAM, and IGA teams, this is no longer a supporting role. It is the primary battleground.
Three decades of security assumptions, invalidated
Every major security category built since the 1990s rests on an implicit assumption: there is time between when an attacker moves and when a defender responds. That is no longer true.
Detection and response assumed breakout time was long enough for an alert to fire and a human to act. Machine-speed attacks eliminate that gap. Detection becomes observational, not preventive.
Vulnerability management assumed you would find and patch critical vulnerabilities first. Mythos does not need critical vulnerabilities (though it can find them at will). It chains the ordinary ones into breach paths no human attacker would have had the patience to construct.
IGA assumed periodic access reviews would catch drift before it became an incident. It breaks entirely against AI agents: faster, multi-identity, non-deterministic, and indifferent to your quarterly attestation cycle. Many are ephemeral by design—spun up, used, and gone before a review ever runs.
Admin-time governance can no longer carry the weight it once did. The governance posture matters. But it is no longer the control. Runtime is.
The patching race is unwinnable
Some practitioners have responded by doubling down on vulnerability management. I have never believed in the cat-and-mouse game as a strategy, and I especially do not believe in it now. The mouse got smarter. It maps the entire maze before it moves, knows where every trap is, and finds seventeen routes to the cheese while you are still watching the first hole. You will not win by building a faster trap. Change where you compete.
A new generation of controls built for machine time
The endpoint market made this transition a decade ago. Antivirus gave way to runtime prevention that intercepts execution before it completes. The tools that survived moved into the execution path, not alongside it. Identity Security is at the same inflection point now. A new generation of platforms is being built around inline enforcement and real-time access decisions at the moment of authentication, including veteran players who went deep on Active Directory and are now extending that foundation into cloud and agentic environments. The premise is the same: the only control point that beats machine-speed attacks operates at machine speed, inside the access flow, before the door opens.
What CISOs and IAM leaders are calibrating differently
1. Runtime is king
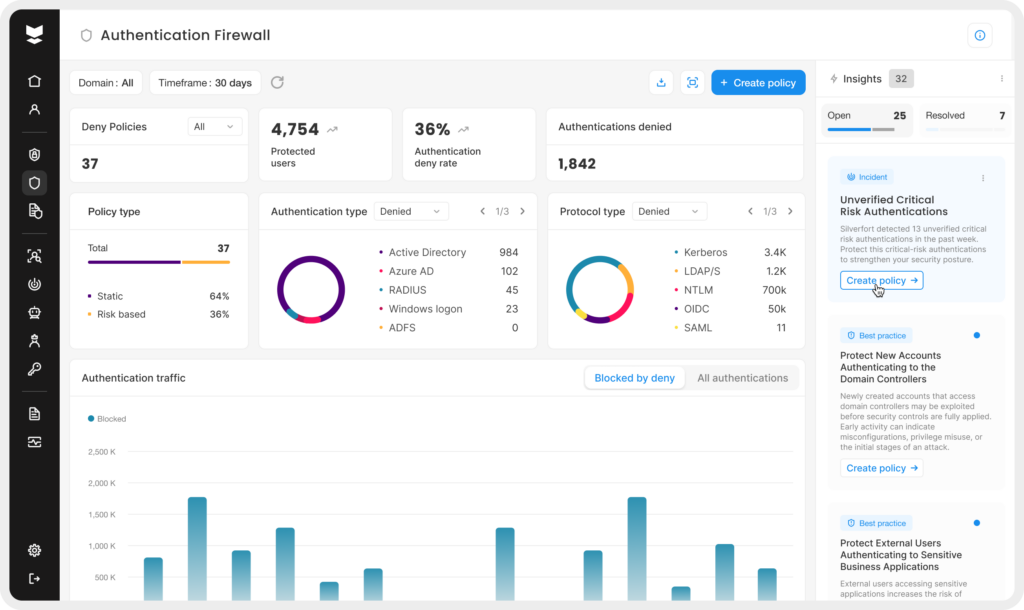
Every authentication request evaluated in real time against dynamic context, and a decision made before access is granted. If a service account that has authenticated to two servers for three years suddenly requests access to a domain controller at 3am, the answer is no (in milliseconds). For IAM and PAM teams, this is the architectural shift that matters most: from provisioning and governance as the primary control to runtime enforcement, with real-time context and dynamic policies feeding it.
2. AI in the access decision loop
The answer to AI-speed attacks is AI in the access decision loop, with identity context fed to it in real time. Intent, behavioral history, asset sensitivity, organizational context, threat signals, the nature of the request. The model makes or recommends decisions: allow, deny, step up, allow with constraints, reroute. Humans stay in the loop for high-risk decisions. AI absorbs what should never have required human judgment.
3. Assume breach as a standard operating mode
Recovery from an AI-agent attack leaves no traditional malware footprint. The forensic trail is in the identity layer: authentication logs, access patterns, privilege use. Build identity snapshots and access state baselines you can roll back to. The organizations running model-based attack simulations against themselves now are the ones who will scope a real incident in hours, not weeks. They will be resilient—not because they got lucky, but because they practiced.
4. Agent identity posture, before the exposure becomes the breach
Most organizations have almost nothing built here. AI agents authenticate with over-privileged accounts, their actions are unattributed, their behavior is baselined against nothing. Every agent transaction must be traceable to an originating human through an identity graph. Intent analysis must be possible: is this action consistent with the agent’s stated purpose? Access decisions cannot be binary. Allow, deny, partial allow, reroute, time-limited access, all at machine speed with full auditability.
5. The perimeter is now everywhere—including the interior
Static credentials and standing privileges were always a risk. Against AI-speed attacks… they are an open door. Coverage must be consistent across every identity type, every environment, every access path. The interior must be held to the same standard as the exterior: no unmonitored credentials, no implicit trust, no gaps an agent can chain into a breach path. PAM can no longer operate as an island—organizations that treat privileged access as a compliance checkbox will find out what that costs.
What Silverfort can do for you
If attacks now execute at machine speed, security controls must operate at the same speed, inside the access flow itself. That is exactly what Silverfort delivers.
Silverfort embeds Identity Security directly into authentication and access flows across all identities, human, machine, and AI agents, and all environments. At the core is Runtime Access Protection (RAP), which integrates natively with existing IAM infrastructure like Active Directory or with agentic platforms, to secure them from within. Instead of relying on detection after-the-fact, Silverfort evaluates, makes dynamic access decisions, and enforces them in real time, before authentication is completed. This is not another visibility or policy layer. It is a centralized control point, inline and at enterprise scale.
In practice, this means:
Stopping threats at the moment of access. Every authentication request is evaluated at runtime against dynamic identity context, behavior, and risk, blocking or stepping up suspicious access before it turns into lateral movement or privilege escalation.
Outpacing attacker speed with inline enforcement. As attack timelines compress, the advantage shifts to whoever can act first. Silverfort runtime protection ensures unauthorized access is stopped before it can propagate.
Securing AI agents as first-class identities. AI agents are treated like any other identity, with the same rigor. Silverfort provides visibility into agent activity, enforces least privilege, and controls actions in real time to prevent misuse, overreach, or unauthorized access.
Eliminating identity blind spots. Silverfort extends protection across all identities and environments, including systems that are traditionally hard to secure, such as legacy infrastructure and homegrown applications.
Bottom line
Mythos is a signal. AI-driven attacks are pushing identity abuse, privilege escalation, and lateral movement into machine time. The patching race is unwinnable. Detection is now forensics. The assumptions that held for thirty years have expired.
For identity and access disciplines, this is the defining moment. Runtime decision-making and enforcement are not optional anymore. The only place left to compete is inside the authentication and access flow, before the door opens, and at the speed the attacker is already moving.
To learn more about the importance of runtime enforcement at scale, register for our upcoming LinkedIn Live event: “Autonomous runtime access control: The future of Identity Security is here.“

