In early May 2022, the Certifried (CVE-2022-26923) vulnerability was published. This vulnerability abuses Kerberos certificate extension and its Active Directory elements. It’s a privilege escalation vulnerability in which a weak user gains domain admin privileges in an Active Directory environment.
How does it work?
The Certifried vulnerability allows an attacker to elevate privileges from a weak user to a domain admin. In short, each user can create up to 10 machine accounts in a domain. An attacker can alter a weaker machine to the target’s computer name and request a malicious certificate on its behalf. Next, the attacker can authenticate as the target computer using the crafted certificate and run malicious code with high privileges. The vulnerability has a wide impact due to its minimal prerequisites. All it requires is a connection to the network and a weak user.
Each identity in AD has attributes. Some of them are unique across the domain, e.g., Service Principal Name (SPN), and some can have duplicates. The attacker creates a weak machine account, abuses its dNSHostName attribute and alters it to the target’s hostname. The attacker then requests a certificate with the Subject Alternative Name (SAN) identical to the target’s hostname. Normally, this attack flow cannot be completed, because changing the dNSHostName must match the SPNs of the server. However, if the SPNs are deleted, then the issue is resolved; it is possible to change the dNSHostName.
The vulnerability also deals with how the domain controller maps a certificate to the identity object in Active Directory during the authentication process. It is possible to request a certificate for Client Authentication purposes and embed the dNSHostName as the SAN.
The returned certificate can now be authenticated to the domain controller using the PKINIT extension and identified as the target host.
One way to exploit this vulnerability, is to authenticate to Active Directory as a target domain controller, and use that to steal the credentials of all the users in the domain.
Mitigation
Microsoft released the May 10 patch for Windows Servers to add another layer of protection to certificate creation and authentication. However, it will only apply to certificates requested after patch installation. Enforcement mode will begin by May 9, 2023.
Silverfort Unified Protection Platform has the capability to inform you of ongoing Certifried attacks, in case any malicious certificates were created before the patch. This latest security guideline regarding Certifried will provide detailed instructions on how to defend against a Certifried attack.
We created a simple Powershell script to automatically collect all data needed for creating a custom filter with Silverfort.
- Please run the following command on a domain workstation powershell
$dc_list = Get-ADDomainController -Filter * | Select-Object Name, ipv4address
write “https://<admin-console>/Logs?deviceOrServer=$($dc_list.ipv4address -join
‘,’)&excludedFilters=deviceOrServer&includeSources=$($dc_list.Name.ToLower() -join ‘,’)&service=krbtgt”
Replace <admin-console> with your Silverfort’s console URL.
- Paste the output in your browser and log in
- Add any known source IP addresses your domain controllers may be using, if they are missing from the automatically-generated list, e.g., addresses of NAT devices.
- Click on Save Filters, give it a name and click Save
- Now that the filters are created, click the cogwheel on the top right of the screen:
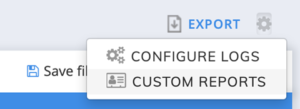
- Then select CUSTOM REPORTS
- Fill in the required details, select the two newly created filters and click Save.
- You will receive regular reports about certified exploits regarding all your domain controllers.
If this filter produces any authentication results, your environment may be under attack. In this case, the domain controllers appearing in the logs might have been compromised and need to be examined. Please verify for each authentication the source hostname matches the source IP. If the IP is unfamiliar, there might be an attempted Certifried attack in your environment. Reach out to us if you need any assistance.

