Active Directory (AD) tiering is nothing new for organizations that need the most secure IT environments, like those in the defense and critical infrastructure spaces. While it is a surprisingly underused approach to partitioning and protecting an organization’s most valuable assets and accounts, it is starting to find its way into more businesses as an effective method to stop privilege escalation attacks in AD.
AD tiering projects frequently go hand in hand with implementing the principle of least privilege to stop lateral movement within a tier. Additionally, they’re often accompanied by the implementation of visibility tooling to provide insights on privileged account and legacy authentication protocol usage, both of which are key to a successful AD security tiering project.
In this blog, we’ll explore the visibility challenges associated with Active Directory (AD) tiering and discuss how Silverfort visibility capabilities help organizations overcome these challenges, making the management of AD tiering simpler and more efficient.
Common Visibility Challenges in AD Tiering
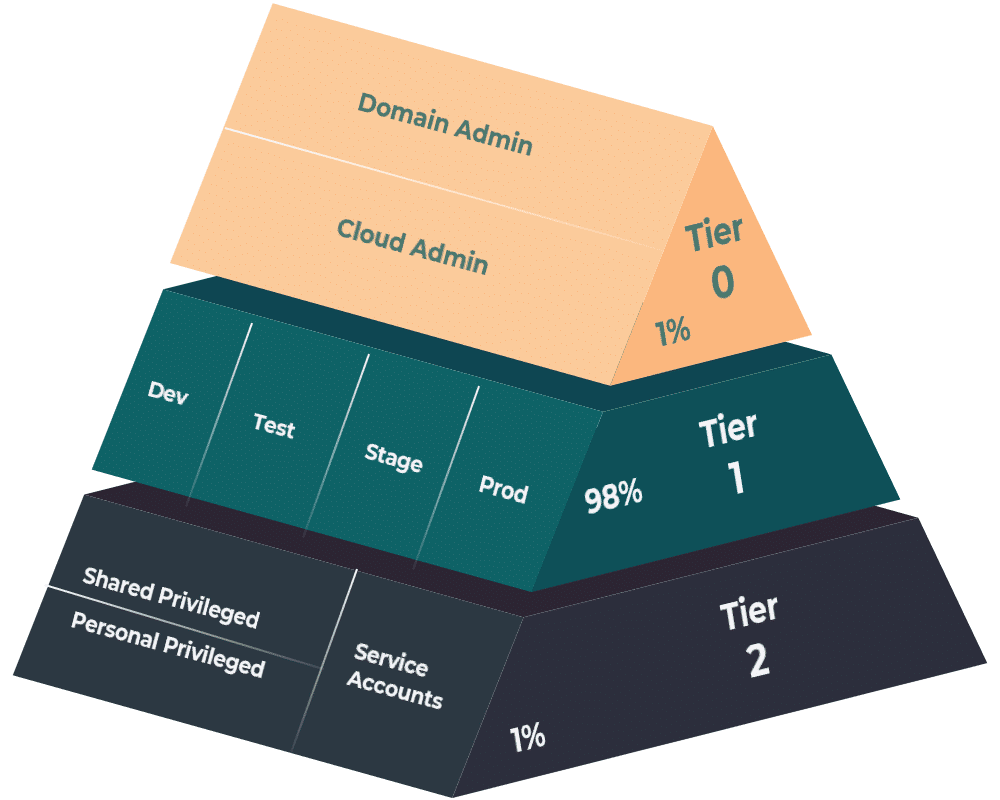
Organizations typically start an AD tiering project by locking down human account access to Tier 0, which includes Domain Controllers, PKI online signing CA, Entra Connect / AD FS. They do this by using Privilege Access Workstations and logon restrictions with group policies and/or authentication policy silos.
However, organizations often struggle to extend this approach beyond Tier 0, crucially leaving Tier 1 – where typically 98% of all admin accounts and privileged service accounts reside (see Figure 1) – without full coverage.
Here are the main challenges that most organizations experience with AD tiering:
Limited Visibility of Privileged Service Accounts
A large portion of service accounts have been in use for a long time and are often overprivileged. In addition, their credentials may be stored unencrypted in the local filesystem, and it can be very challenging to understand exactly where and when they are used.
Insufficient visibility of account mapping
It is essential to consider what resources are accessed by each privileged user when designing a model of least privileged access. These results then need to be validated and sanitized before implementing them as access rules.
Lack of visibility of legacy protocol usage
Ideally, all privileged users should be members of the “Protected Users” group, which disables password caching and legacy protocols. Prior to enabling this group membership, it is necessary to obtain complete visibility into the usage of legacy authentication protocols by these privileged users in order to measure the potential impact and implement remediation measures.
For the above reasons, organizations that have started their AD Tiering model journey typically manage to secure Tier 0 for their admin user accounts but get stuck trying to extend it to Tier 1.
How Silverfort Helps with AD Tiering
Silverfort can enhance AD tiering by offering extensive visibility and control over user access across the organization. It continuously monitors authentication and access activities, assigning risk indicators and scores to users and machines based on their behavior patterns. This process helps identify and manage access to high-risk or high-value assets, which is crucial for AD tiering. Additionally, Silverfort’s integration with Azure AD provides further insights into user behavior and risk, supporting the implementation of an effective AD tiering strategy.
Complete Visibility Across AD Environment
Once deployed, Silverfort will get real-time visibility into domain-based authentications and collect the metadata for every authentication.
Silverfort also offers the ability to scan for attack surfaces and misconfigurations and provides other metrics relevant to the security and health of your Active Directory deployment. Most of these metrics are presented as KPIs in dashboards, live alerts that can be acted upon, or high-level reports that can be used to provide management with an overview of Active Directory risk.
Here are some examples of Silverfort capabilities relevant for visibility on AD Tiering:
Detection of Privileged Accounts
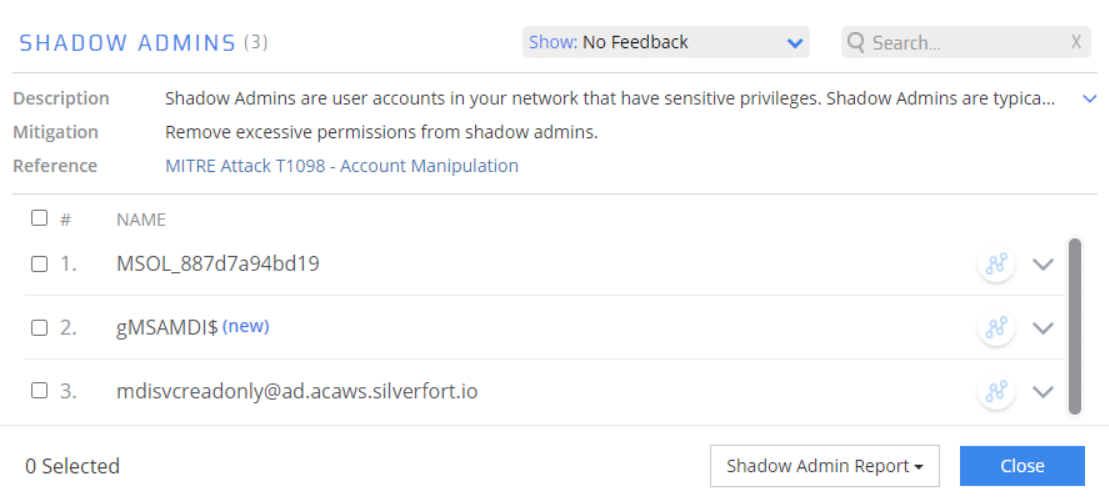
To detect/monitor the user scope for Tier 0, Silverfort can quickly provide an inventory of all relevant accounts using our risk indicators “Domain Administrators”, “Privileged Users” and “Shadow admins”.
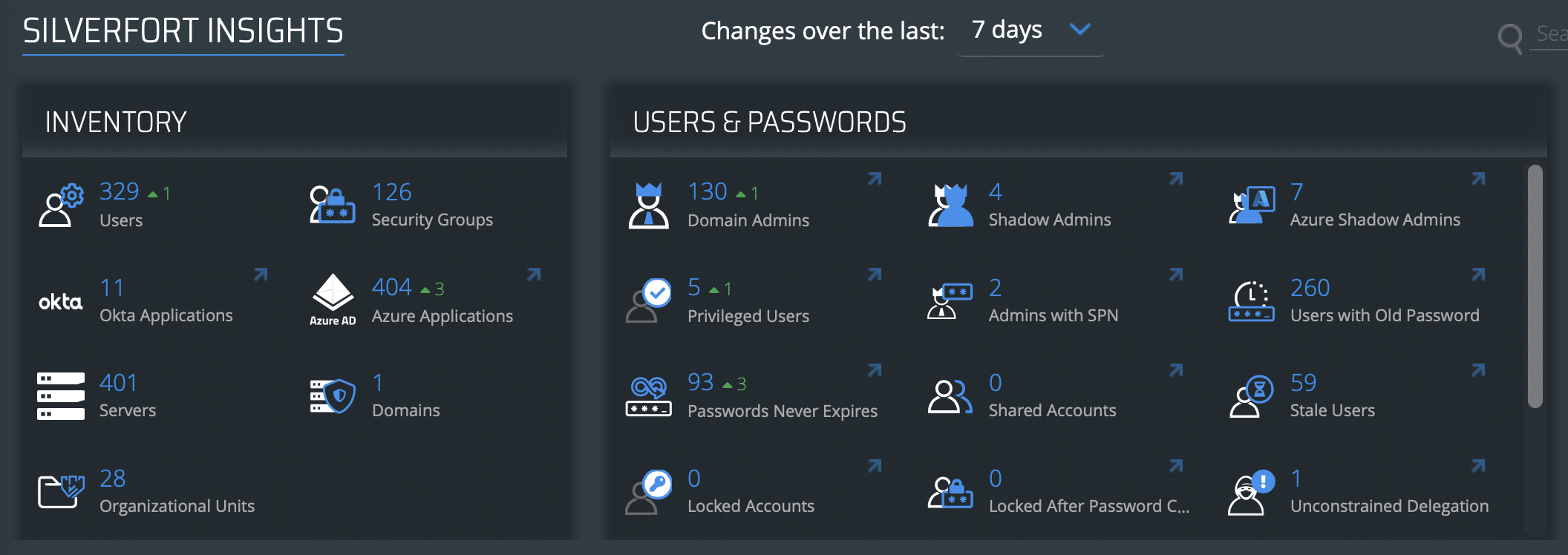
Clicking any of the relevant KPIs will provide a detailed list of flagged accounts, including a short description of the risk, how to mitigate it, and a link to the relevant article in the Mitre ATT&CK framework.
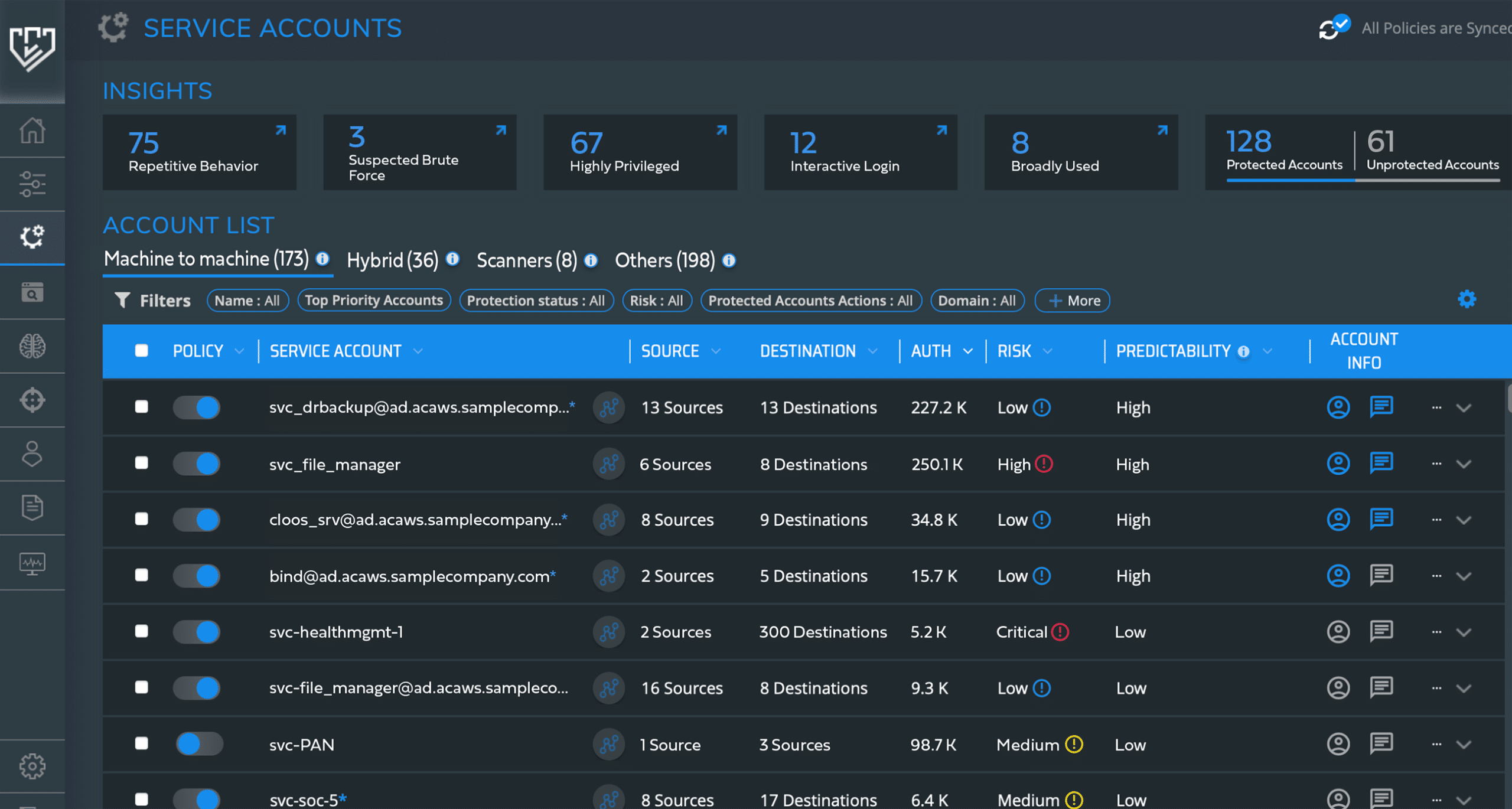
Detection of Service Accounts
Visibility into the usage of Active Directory service accounts is often lacking. Silverfort makes it very easy to quickly get an overview of all service account usage, as well as relevant KPIs such as privileged service accounts, interactive logon (dual use), and risk level based on the attack surface and any observed attacks or unusual behavior.
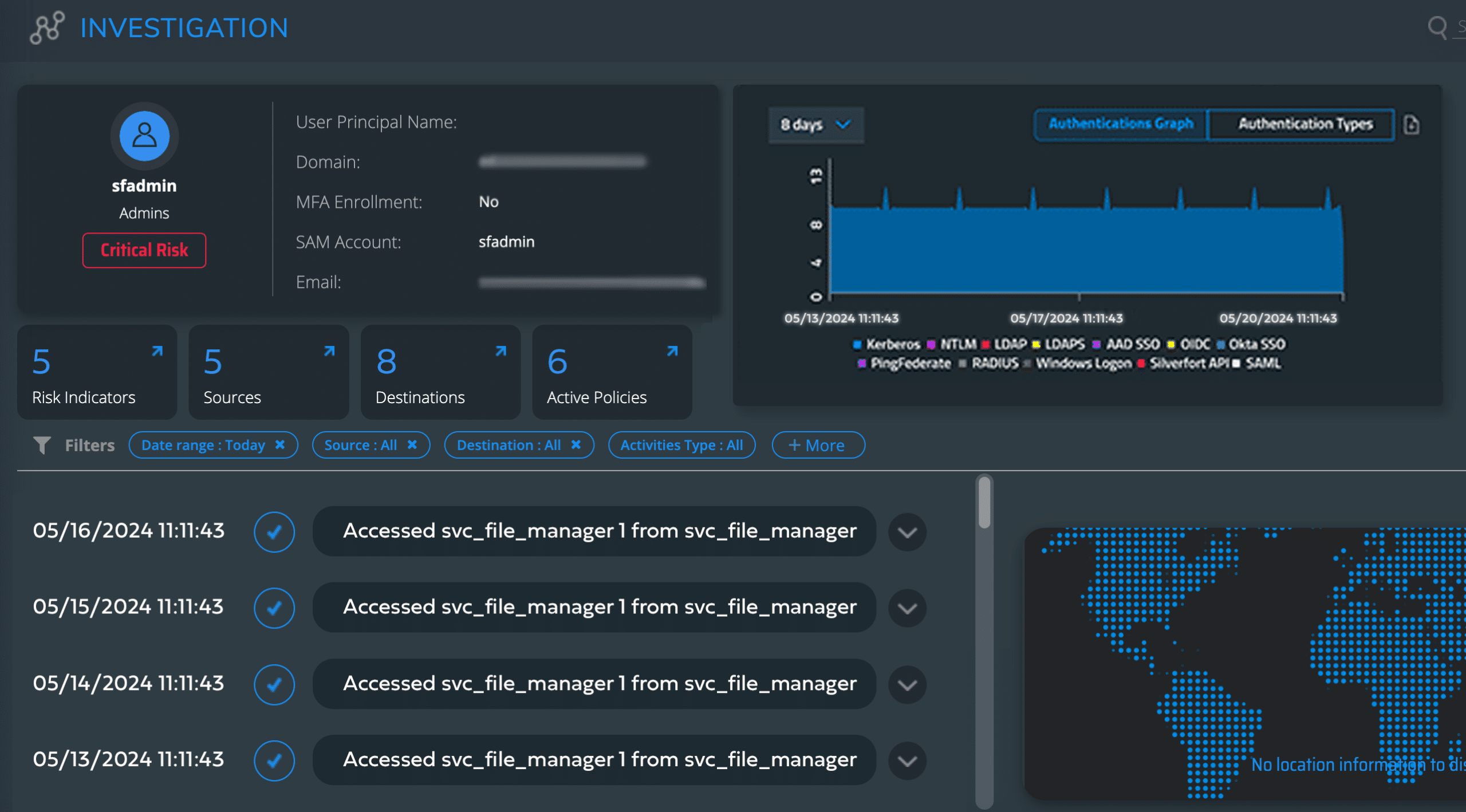
Investigate Service Account Activities
For each Active Directory account of interest, Silverfort’s investigation page provides detailed KPIs providing information where the account is used (Sources), as well as any authentications to destination network services (Targets). This information is essential for defining the scope to implement least privilege using policies.
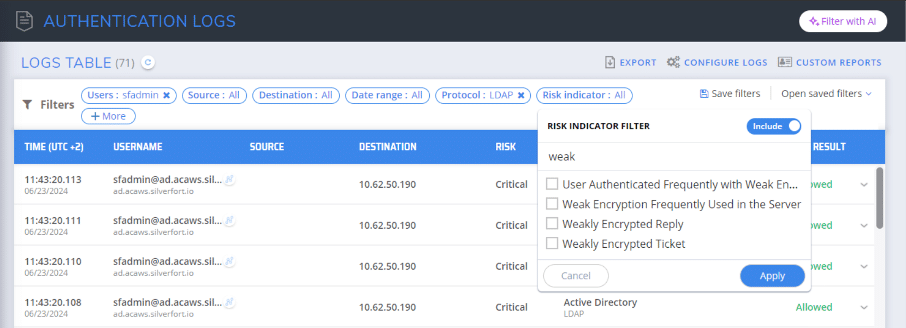
Advanced Authentication Logs
Silverfort’s authentication log with built-in parsers for weak encryption protocols allows for quick identification of authentications that should not be used by privileged users. With this information, legacy authentications can be eliminated or reduced to an absolute minimum. Privileged accounts can also be added to the “Protected Users” group in Active Directory, with good visibility on the possible impact of this action.
Identity Security & Posture Management
The Threat Detection dashboard in Silverfort gives an overview of Active Directory attack surface management, using KPIs for common misconfigurations and other steps that should be taken to reduce the attack surface. Commonly detected issues should be addressed, especially when they concern privileged accounts or resources in Tier 0 or Tier 1.

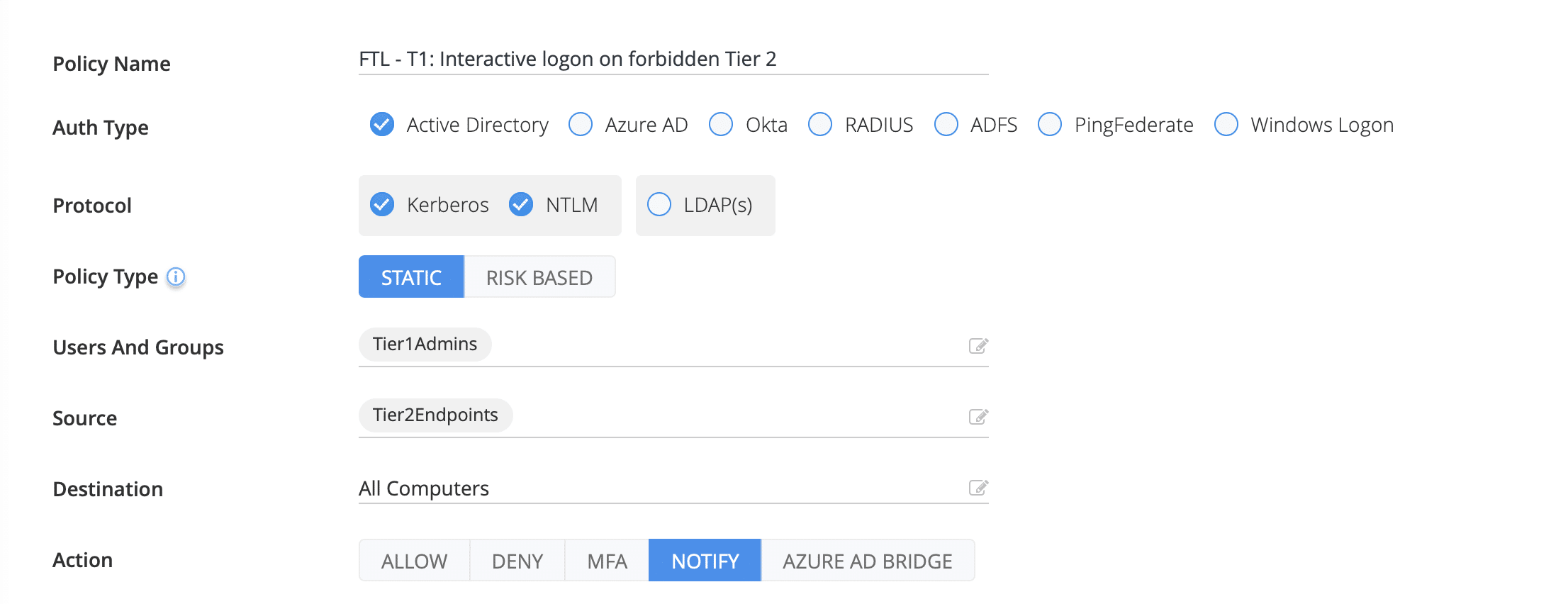
Notification Access Policies
Once asset and account tiers have been established and organized using dedicated OUs or AD groups, it’s easy to create authentication policies to get real-time alerts of inappropriate account usage across tiers and daily reports on their occurrence.
Real-Time Visibility is Essential for Effective AD Tiering Management
Innovations by Silverfort around the visibility of Active Directory authentication allow for a simple yet very effective approach to accelerate the deployment of Active Directory Tiering. With relatively little effort for deployment and configuration, organizations can gain insights into account usage, attack surface, and compliance with tiering policies, as well as user/service account and computer/resource risk.
While there’s no magical solution to rolling out tiering across all Active Directory assets in an organization, Silverfort makes the task significantly easier. Read our next blog in the AD tiering series, where we highlight the specific protection challenges associated with AD tiering and how Silverfort’s enforcement capabilities can effectively address these challenges and strengthen your AD environment.