Uncompromising security for Palo Alto VPN with Silverfort’s seamless MFA solution.
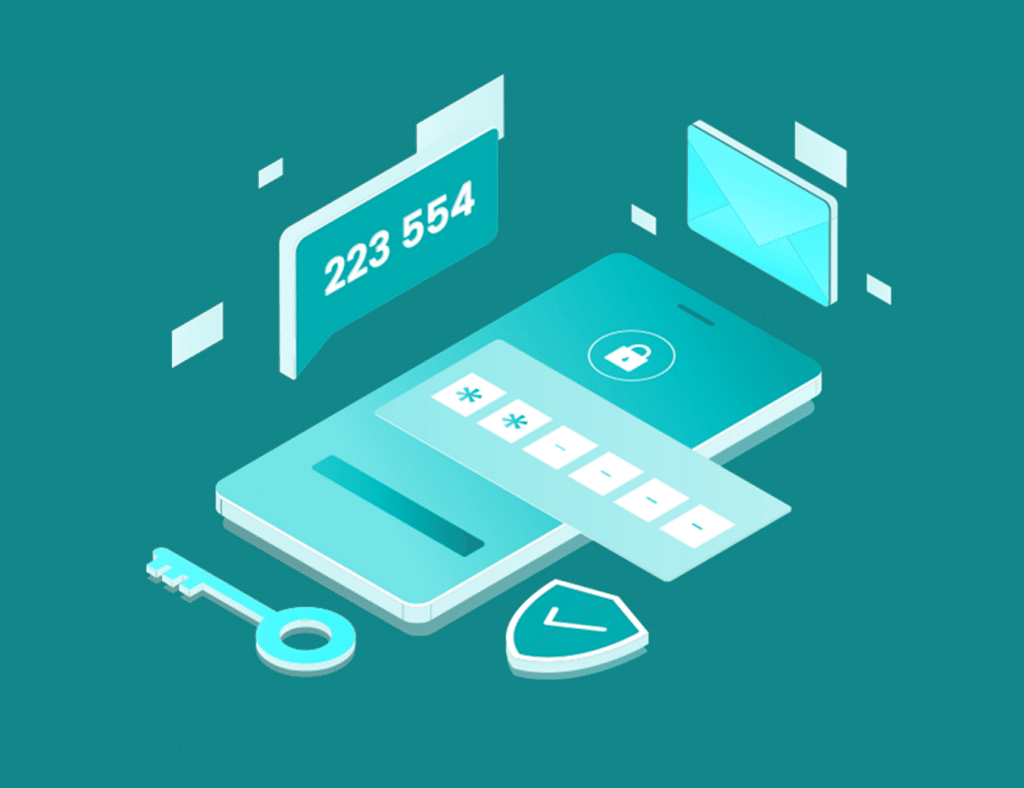
Silverfort provides a secure and seamless multi-factor authentication (MFA) solution for Palo Alto VPN. Using advanced AI technology, Silverfort can authenticate users and devices in real-time, providing continuous protection against account takeover attacks, phishing, and other cyber threats.
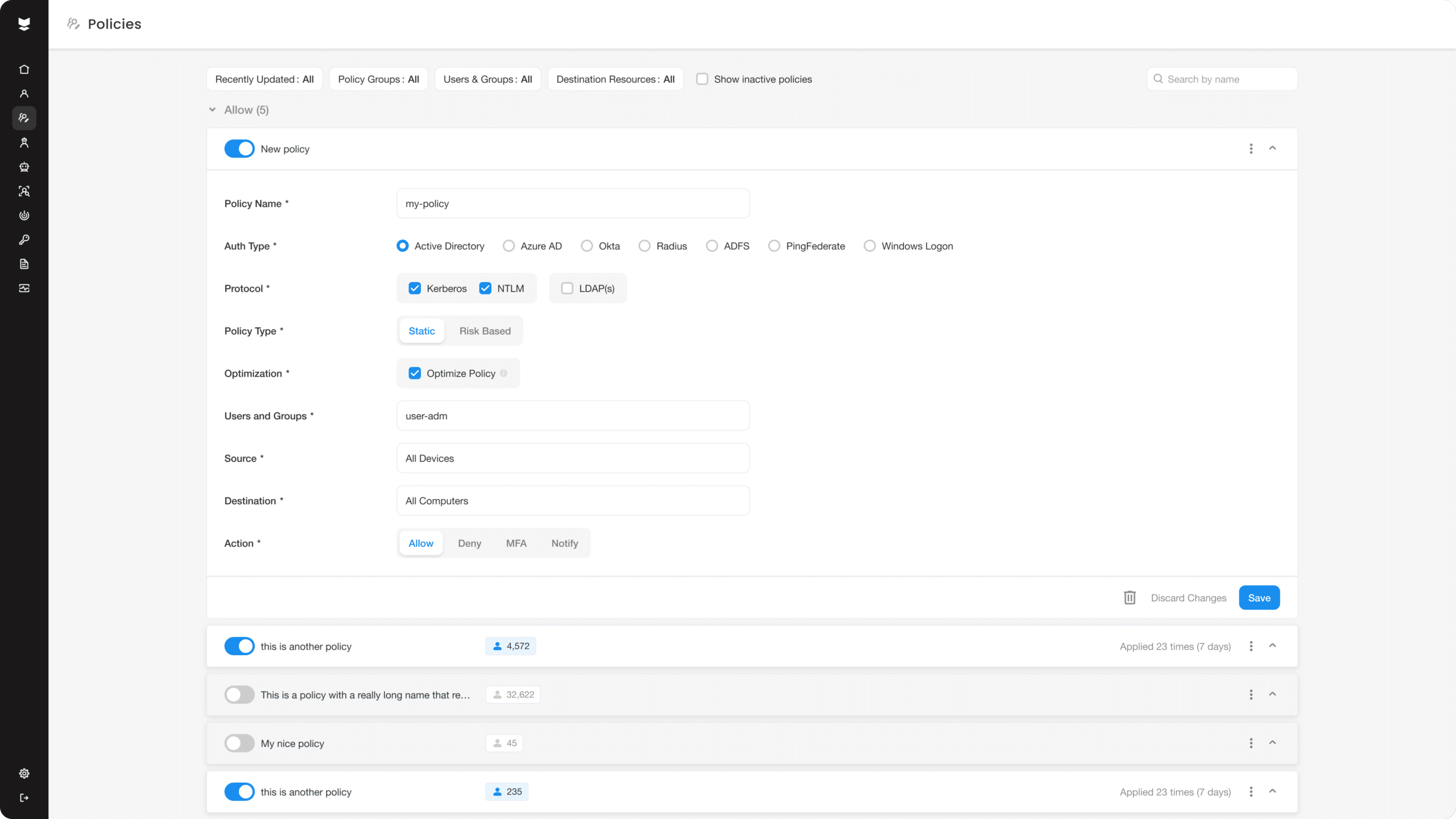
Silverfort’s agentless and proxyless architecture allows it to secure all user resources without blind spots, including Palo Alto VPNs. It can enforce adaptive policies and advanced secure access controls across all resources, access interfaces, and users in the hybrid environment.
Integrating Silverfort’s MFA with a Palo Alto VPN ensures that users accessing the network through the VPN must authenticate using more than just their primary credentials, such as through a one-time passcode, a mobile app notification, or other MFA methods.