Secure your legacy applications with Silverfort: multi-factor authentication made simple.
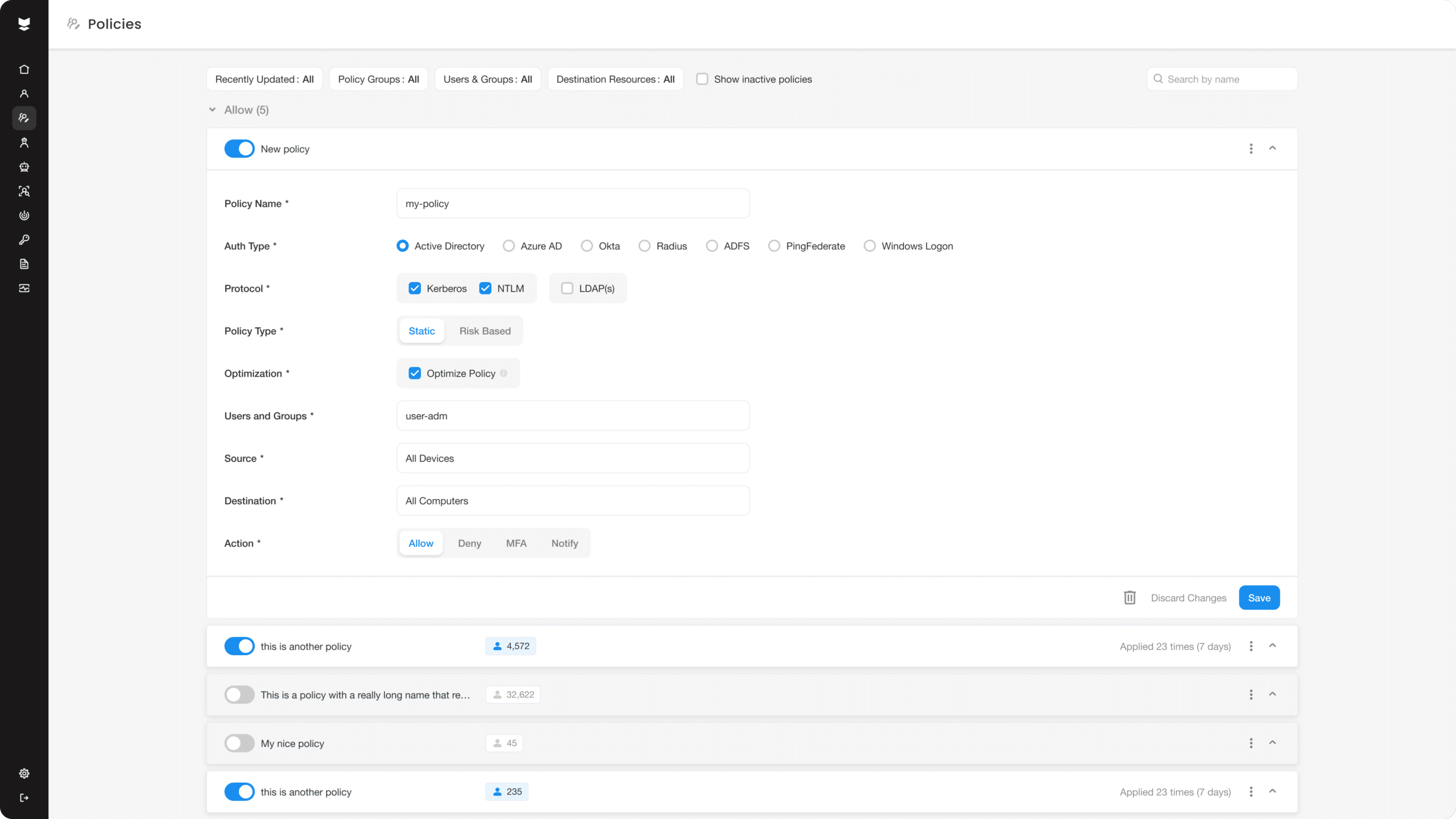
Silverfort enables companies to enhance their security posture without requiring any changes to the existing infrastructure or moving data to the cloud. The solution is simple to deploy, highly scalable, and provides end-to-end protection to users accessing legacy systems, ensuring that only authorized personnel can access critical applications and data. With Silverfort, companies can add an extra layer of security to their legacy systems, making them less vulnerable to cyber attacks and ensuring compliance with regulatory requirements.