With 91% of organizations classifying Identity Security initiatives as a priority in the next 12-24 months, and 87% planning to increase spending on workforce identity solutions, knowing what to look for in emerging Identity Security products and the outcomes they should deliver is now crucial.
Yet most organizations are still struggling to answer these vital questions:
- What exactly should I expect from an Identity Security platform?
- What are the expected outcomes of a modern Identity Security strategy?
- What are the practical steps I can take to mature my Identity Security program and how do I make those steps actionable and feasible?
This is where a clear playbook that defines what Identity Security is (and is not) can provide support. As Identity Security matures into its own category, it’s time we had a reliable standard for what to expect in the “Identity Security” stack – and how to get there.
We’ll address the “how” in a moment, but first: “What” is Identity Security?
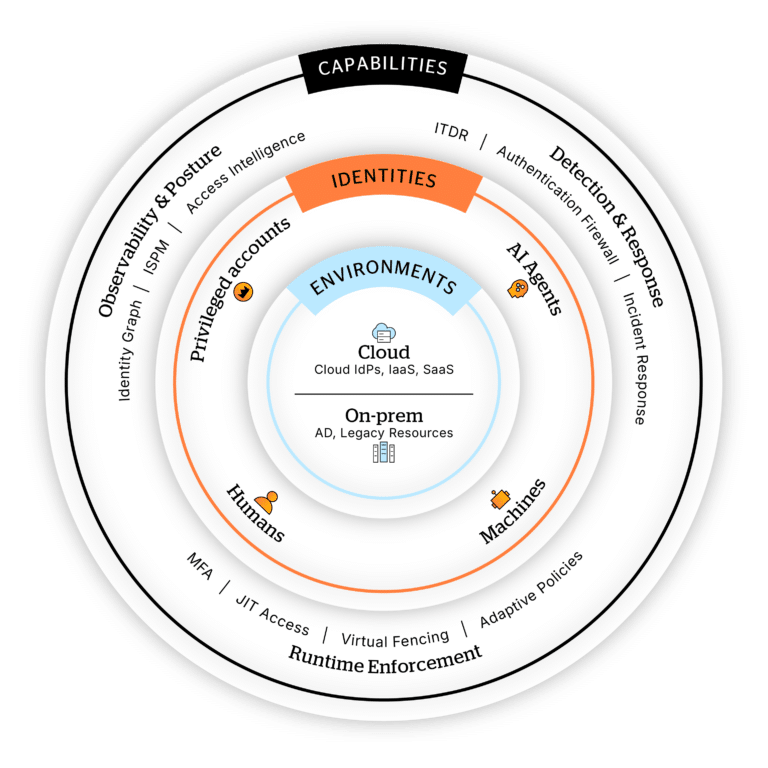
The core capabilities in a complete Identity Security stack
Identity Security is a vendor‑agnostic control plane that:
- Sits atop identity infrastructure, not inside.
- Covers all identities across all environments.
- Brings together visibility, intelligence, and real‑time enforcement in one layer.
Identity Security should function as an independent security layer, integrated across all environments and protecting every identity type—human, machine, and AI. Continuous protection depends on core capabilities like unified visibility, intelligence, detection, response, and inline enforcement. Anything less may leave an identity type unprotected, or a system vulnerable to compromise.
Complete Identity Security does this with three core capabilities:
- Deep observability and posture management across the entire identity infrastructure—cloud and on-prem.
- Detection and response, with identity-first incident response built-in.
- Real-time inline enforcement and controls, such as step-up authentication, Just-in-Time access, identity segmentation and adaptive policies.
Identity Security is only possible when environments, identities, and capabilities work together.
How do I operationalize Identity Security?
This is where the IDEAL Identity Security Framework comes into play. Think about it: We’re already using frameworks to achieve success and define scope in cybersecurity, like MITRE ATT&CK and NIST CSF. In fact, according to MITRE, “More than 80% of North American organizations said ATT&CK is ‘critical’ or ‘very important’ for their security operations strategy.”
Based on successful Identity Security programs across hundreds of organizations, the IDEAL Framework is a practical operating model that incorporates the core capabilities needed to protect every identity everywhere.
It consists of five foundational pillars:
- Integrate: Be everywhere your identities are
- Discover: See, understand, and contextualize every identity
- Enforce: Protect every identity at runtime
- Act: Detect and respond to threats immediately
- Lightweight: Prioritize easy, fast, non-disruptive deployment
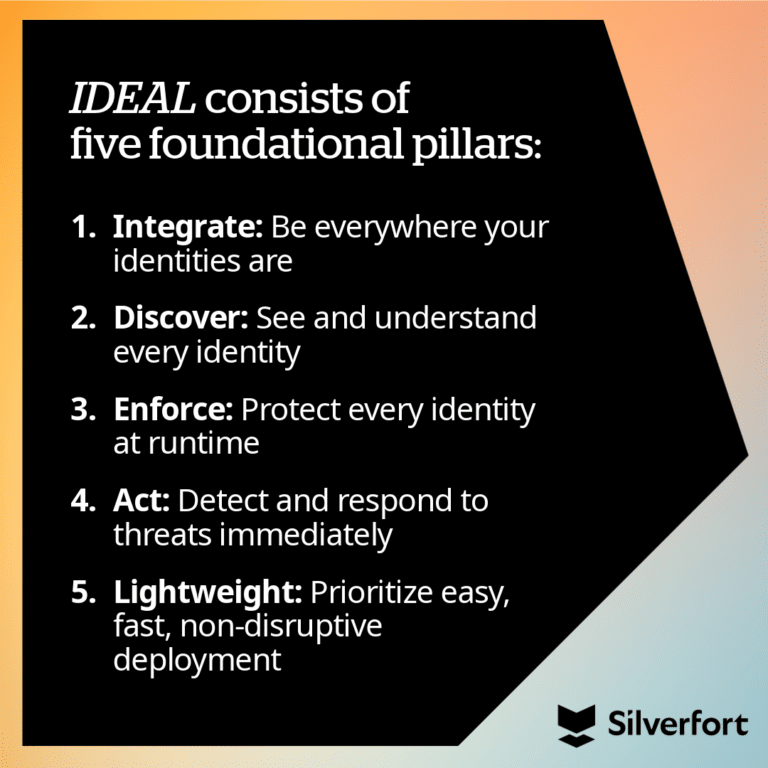
Action plans and outcomes within the framework
Together, the pillars put a 360-degree Identity Security strategy into place: one that can bridge the needs of identity and security teams, adapt to modern threats, and provide consistent security across hybrid infrastructure. Let’s explore each pillar in detail.
The Identity Security Playbook
Use the IDEAL Framework to build a sustainable, effective Identity Security strategy

Integrate: Be everywhere
Chances are your organization is a mix of old and new—from on-prem applications to SaaS, from AWS to AI agents. With the number (and variety) of identities your team needs to identify and secure across different systems, it’s important to integrate a unified security layer on top of all the infrastructure while keeping your business running. Network and cloud underwent similar transformations; for example, CNAPPs solve the “one-layer” security problem for multi-cloud organizations.
The same must be done for identities. Identity is the perimeter and attackers live in the seams between siloed systems that don’t share risk insights.
The message behind “being everywhere” is simple: Identity Security is about connecting to every identity source and authentication path so that you can enforce security in real –time.
Action plan:
- Consolidate, consolidate, consolidate: Find an Identity Security platform that covers all identities everywhere without requiring changes to existing IAM. This must protect access to on-prem resources, too. Active Directory is still a prime target for threat actors in 2026, and if left unchecked, can create lateral movement risk and enable privilege escalation.
- Use the power of consolidation to centralize policies, visualize relationships, gain visibility into authentication and authorization events, and correlate identity activity across environments.
- Illuminate hidden risky access paths, over-privileged identities, and misconfigurations to tighten posture.
- Prioritize runtime-level capabilities to stop threats in their tracks—before they become incidents or breaches.
Outcome: Complete coverage across all environments and all identity types, built on a single source of truth.
eBook
Active Directory exposed: Protecting the heart of enterprise identity
- 5 inherited security gaps in AD
- Why it's time to treat AD as more than just IT hygiene
- How to modernize your AD Security strategy

Discover: See, understand, and contextualize every identity
Hybrid environments generate massive identity sprawl that accumulates risk and quietly builds tech debt. Unfortunately, you can’t secure what you can’t see, so it’s critical to continuously discover, monitor, and analyze identities and their activity.
Action plan:
- Use a platform that continuously finds and classifies identities—workforce, privileged, third-party, non-human identities like service accounts, and AI agents—across the entire hybrid environment.
- Map identities to their privileges, entitlements, and actual access activity to reveal excessive privileges or dormant accounts, shadow admins, misconfigurations, and unfamiliar access patterns.
- Track how and where identities authenticate to uncover hidden risks and suspicious behavior. For non-human identities and AI agents, this visibility is the foundation for enforcing real-time controls without breaking automation.
Outcome: Comprehensive identity visibility and intelligence that draws a clear map of all users and accounts, their privileges, access paths, and risks.
Enforce: Protect every identity at runtime
Once threat actors gain a foothold, lateral movement and privilege escalation can happen in seconds, often without triggering endpoint defenses or touching the network. This makes preventative, policy-driven enforcement at the identity level critical to set the rules for what each identity is allowed to do.
Importantly, this must apply to every identity, not just privileged ones. Traditional PAM does not cover every identity with privileged access that could be a way into your environment—and it often takes years to deploy.
Instead, capabilities like adaptive MFA and Runtime Access Protection close security gaps and enforce protection here and now.
Action plan:
- Enforce customizable, adaptive, universal policies rooted in context before granting access to systems and resources.
- Ensure all privileged access is secured at scale, using capabilities like adaptive MFA, virtual fencing, Least Privilege policies, and Just-in-Time (JIT) access to optimize protection and speed.
- Implement an Identity Firewall to proactively segment identities during a live incident to stop the spread of the attack.
Outcome: Continuous control driven by always-on, policy-driven access decisions that evaluate risk upfront and prevent common attack techniques like lateral movement.
Act: Detect and respond to threats immediately
When threat actors use legitimate credentials and access paths to blend in, catching signals in your SIEM can feel like finding a needle in a haystack. Instead, identity misuse must be detected in real time at the point of the access, so teams can act accordingly.
This is where modern solutions like Identity Threat Detection and Response (ITDR) and the SOC come together to baseline what’s normal, what should be stopped, and what should be flagged for further investigation.
Action plan:
- Use an Identity Security platform that enables the SOC to continuously monitor and analyze identity behavior.
- Ensure your ITDR solution provides remediation recommendations (automated wherever possible) to triage quickly and accelerate recovery.
- Integrate enriched identity context into SIEM, SOAR, and IR workflows for a fast, coordinated response across security and IT teams.
- Model baseline behaviors for AI agents and non-human identities, so anomalies stand out clearly while avoiding disruption to legitimate workflows and automations.
Outcome: Identity-driven containment that stops compromised accounts from being used maliciously and empowers teams to recover fast.
Lightweight: Easy to deploy and run
Modern security must be lightweight by design. If your Identity Security program can’t give you visibility right away, it’s already too slow. You need to be able to deploy quickly, scale easily, and operate without adding friction.
As mentioned before, this is why seamless integration with your existing IAM infrastructure is a must. You shouldn’t have to change anything that could be disruptive to productivity in the name of Identity Security.
Action plan:
- Choose an Identity Security platform that doesn’t require code changes, agents, or proxies.
- Demand fast time-to-value so your deployments are measured in days or weeks rather than months or years.
- Prioritize operating at scale—as your identity surface increases, your visibility and security should scale with it.
- Find a solution that helps you right-size current investments so you can decommission unused licenses and reduce costs.
Outcome: Cost reduction fueled by rapid deployment, simplified operations, and tool consolidation.
See how Silverfort provides 17x faster deployment
Compared to traditional solutions on average
Where will you invest to align with the IDEAL Framework?
When the IDEAL capabilities are fully implemented, they produce measurable outcomes that set the stage for a resilient, identity-first security posture.
Now that you have a clear action plan for each pillar, we invite you to see how they work using real-world use cases.
In the Identity Security Playbook, you’ll see how the IDEAL Framework helps CISOs, identity, and security teams to:
- Protect privileged access
- Stop and contain attacks
- Adopt AI agents securely
- Secure non-human identities like service accounts
- Shrink the identity attack surface
- Maintain compliance and build audit-ready Identity Security
Get your copy of the Playbook to discover the IDEAL Framework in action.


