If you work in education IT security, the news about Canvas hit differently. Instructure, the company behind the learning management system used by more than 8,000 universities and schools, suffered a major breach, with reports suggesting up to 275 million users may be affected. It’s one of the largest breaches in education history.
I’ve seen this pattern before. And I have real empathy for the teams right now fielding calls from leadership, parents, and the press all at once.
While initial reporting focused on credential-based access through Instructure’s Salesforce environment, the full picture shows a more complex attack chain. The April 2026 breach exploited Free-For-Teacher accounts—a program Instructure has since permanently shut down—as the primary entry point. This is distinct from the September 2025 breach, which involved social engineering targeting Instructure’s Salesforce instance.
When Instructure was previously targeted in September 2025, ShinyHunters used social engineering to breach Instructure’s Salesforce business environment—accessing business contact information, but not student or customer data from the Canvas platform. However, the April 2026 breach is categorically different: it targeted Canvas production systems directly, compromising private messages, names, email addresses, and student ID numbers for up to 275 million users. Different systems. Different impact. Same threat actor. This shows that ShinyHunters views Instructure as a high-value target worth revisiting—and any institution relying on Canvas should assume the same targeting could happen again.
For many institutions, Canvas is Salesforce-connected. So are most modern EdTech platforms.
The question every institution should be asking isn't just “Was our student data in Instructure's systems?” It's “What do our SaaS vendors have access to in our environment, through integrations we may not even be monitoring?”
Timeline: How the breach unfolded
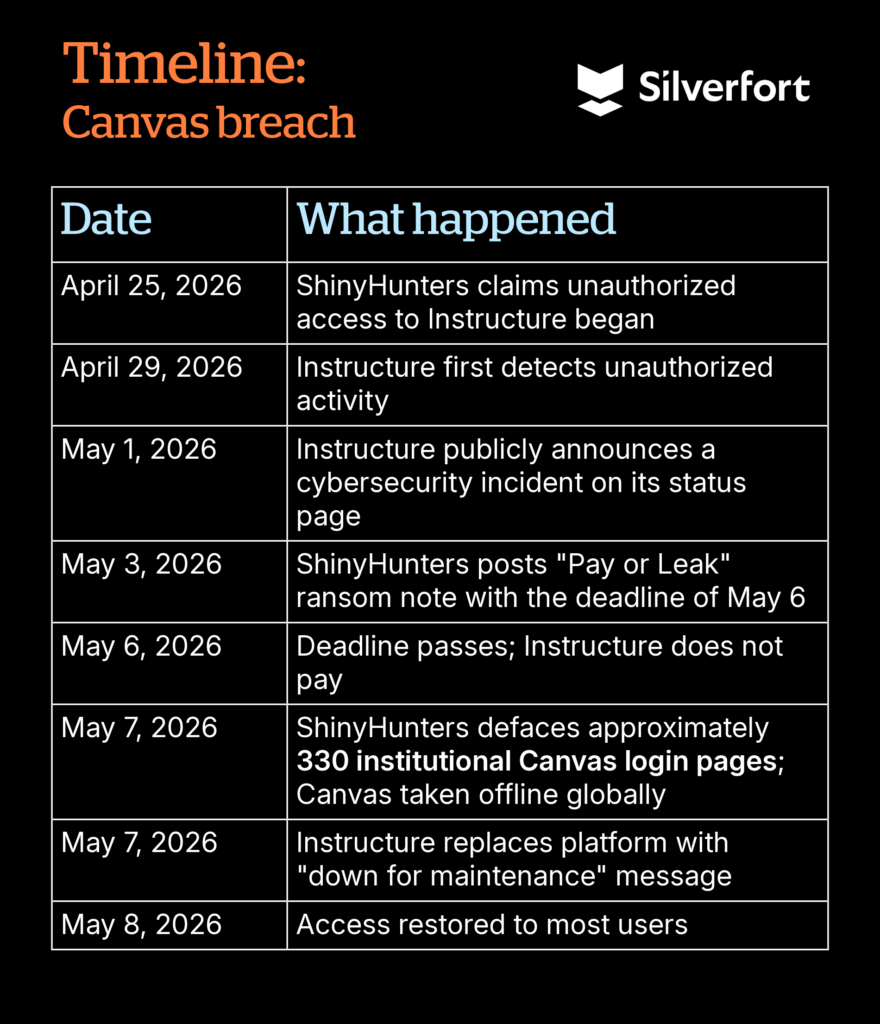
For affected institutions, this meant final exams postponed, administrative systems locked down, and security teams working around the clock—often with incomplete information.
Understanding the Canvas attack by ShinyHunters: SaaS integrations are identity, too
Groups like ShinyHunters and Scattered Spider, whose tactics we’ve analyzed in-depth, rarely need to find a technical vulnerability when they can use a valid credential. They look for the path of least resistance: an OAuth token with excessive scope, a service account with standing privileges, or an MFA gap on a legacy system.
How ShinyHunters bypasses MFA: AiTM & device code phishing
Security researchers have documented three primary techniques ShinyHunters uses:
Vishing + AiTM (Adversary-in-the-Middle) phishing
An attacker impersonating IT support calls a target employee and directs them to a victim-branded phishing page. As the user enters credentials and MFA codes, the page relays them in real-time to the legitimate identity provider—which sees a normal login and approves access. Traditional MFA bypassed.
Vishing + device code phishing
Attackers trick users into entering a code on Microsoft’s (or another IdP’s) legitimate verification page. This grants an OAuth token directly—not a password or MFA code. This technique defeats all forms of MFA, including passkeys, because it targets the authorization layer rather than the login flow.
OAuth supply chain exploitation
Rather than attacking an institution directly, attackers compromise a SaaS vendor’s OAuth tokens, then use those tokens to access the downstream environment. This is exactly the pattern we saw in the Salesloft Drift breach—and appears relevant here.
The common thread: post-authentication behavior is the new battleground. If your security tools only flag the initial login, you’ll miss the lateral movement that follows.
Modern education environments are deeply integrated. For example, your LMS may connect to your Salesforce CRM, which then connects to your student information system, which connects to your identity provider. Each of those integrations is an OAuth token, an API key, or a service account credential. Each one is a non-human identity (NHI). And in most environments, those identities have broad access, no MFA, minimal monitoring, and no one clearly responsible for their security.
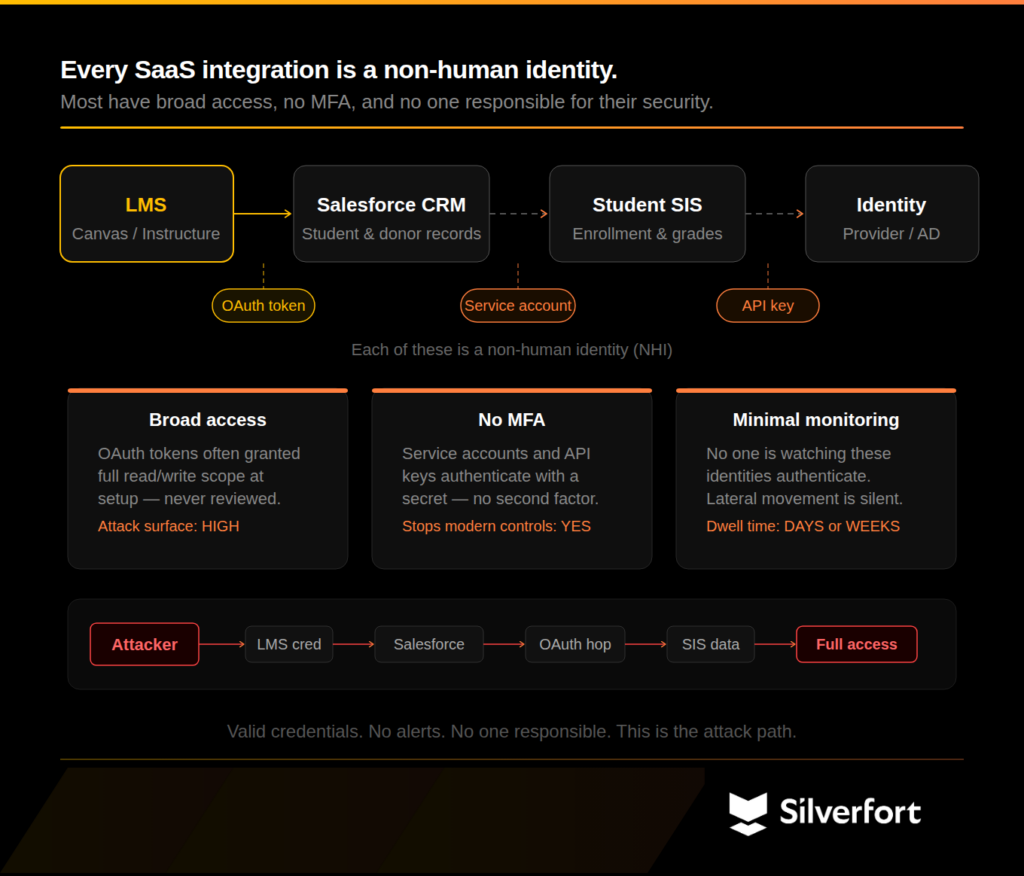
Once attackers are in with valid credentials, they move laterally, quietly, and fast. By the time the alert fires, they’ve often been in the environment for days.
What you can do now to protect against future identity breach attempts
Audit your SaaS integration credentials
Which of your vendors have OAuth tokens or API credentials with access to your Salesforce environment, your IdP, or your student data systems? These are NHIs and should be treated with the same rigor as any privileged human account: tightly scoped, monitored, and rotated. Most institutions we talk to don’t know the full answer and lack visibility into access across their environment. That’s the first thing to fix.
Get visibility into your service accounts
Service accounts across your on-prem and hybrid environment carry standing privileges, no MFA, and little monitoring. Start by understanding what’s in your environment, not just the accounts you know about, but the ones that have quietly accumulated access over years of system changes. You can’t protect what you can’t see.
Enforce MFA everywhere—especially where it’s hardest
Most institutions have MFA on cloud apps and VPN. But attackers don’t use the front door. They use legacy protocols, i.e., NTLM, Kerberos, PowerShell, that bypass modern controls entirely. Extending MFA to cover these protocols without disrupting operations is one of the most impactful things you can do.
Prepare for targeted phishing using stolen data
The nature of the stolen data significantly increases risk. Because exposed information includes private messages referencing real courses, student names, instructor details, and institutional relationships, attackers can craft highly personalized phishing communications that reference actual courses and conversations. Generic phishing training isn’t enough. Train users to hover over links, verify requests via out-of-band channels, and treat any communication referencing specific Canvas courses with extra scrutiny. Also monitor for new phishing domains spoofing Canvas branding.
PRACTICAL GUIDE
Extending MFA everywhere
How to close legacy and on-prem authentication gaps

Watch for lateral movement in real-time
The window between initial compromise and significant damage is often hours. Identity Threat Detection and Response (ITDR) gives your SOC visibility into anomalous authentication behavior such as unusual access times, protocol mismatches, accounts touching systems they’ve never reached before, so you can act before the blast radius grows.
Consider your regulatory obligations
Beyond the technical response, affected institutions face significant compliance requirements. Because Canvas serves K-12 districts, colleges, universities, and education ministries, the breach implicates:
- FERPA (Family Educational Rights and Privacy Act): Places notification burden on the institution, not the vendor
- COPPA (Children’s Online Privacy Protection Act): Relevant for K-12 districts handling data on minors
- Approximately 130 state student-privacy statutes with varying notification timelines and requirements
Institutions that delay response may face not just reputational damage, but legal and regulatory consequences. Class action lawsuits are already being investigated against Instructure—meaning your institution could face litigation as well. Consult your legal team now on notification requirements and documentation obligations.
What to think about next: Shrinking your identity attack surface
Once you’ve addressed the most urgent exposure, the longer-term work is about shrinking your identity attack surface systematically. Two capabilities matter here.
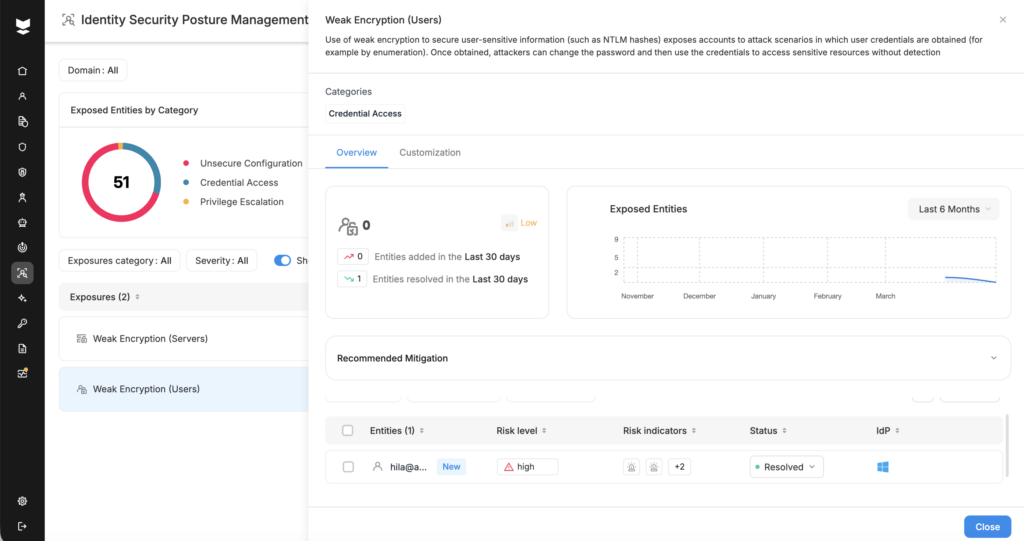
Identity Security Posture Management (ISPM) surfaces the risk that has accumulated over years: stale accounts, misconfigured MFA policies, legacy protocol usage, over-privileged service accounts. It gives your team a continuous, prioritized view of what to fix and in what order. That’s the difference between reacting to breaches and reducing the conditions that make them possible.
Access Intelligence goes further mapping every access path across your environment, revealing privilege sprawl, unused entitlements, and hidden routes that traditional IAM tools miss. For EDU environments with years of accumulated access rights across staff, faculty, and dozens of integrated systems, that visibility is what makes least privilege practical rather than theoretical.
Institutions that build this posture discipline are the ones that don’t end up in the headlines the next time a vendor is breached.
A note on what Silverfort has seen
Silverfort works with institutions including Pembroke College, Cambridge and University of the Pacific on exactly these challenges. We’ve also built and executed identity incident response playbooks against ShinyHunters and Scattered Spider in real time… not as theory, but during active attacks.
If you’re wondering where your institution stands, let’s talk it through. Book a call with our team today.
Want to learn more about Identity Security for education?
Read case studies and learn how Silverfort helps you protect every dimension of identity.

