
Visibility and protection without limits.
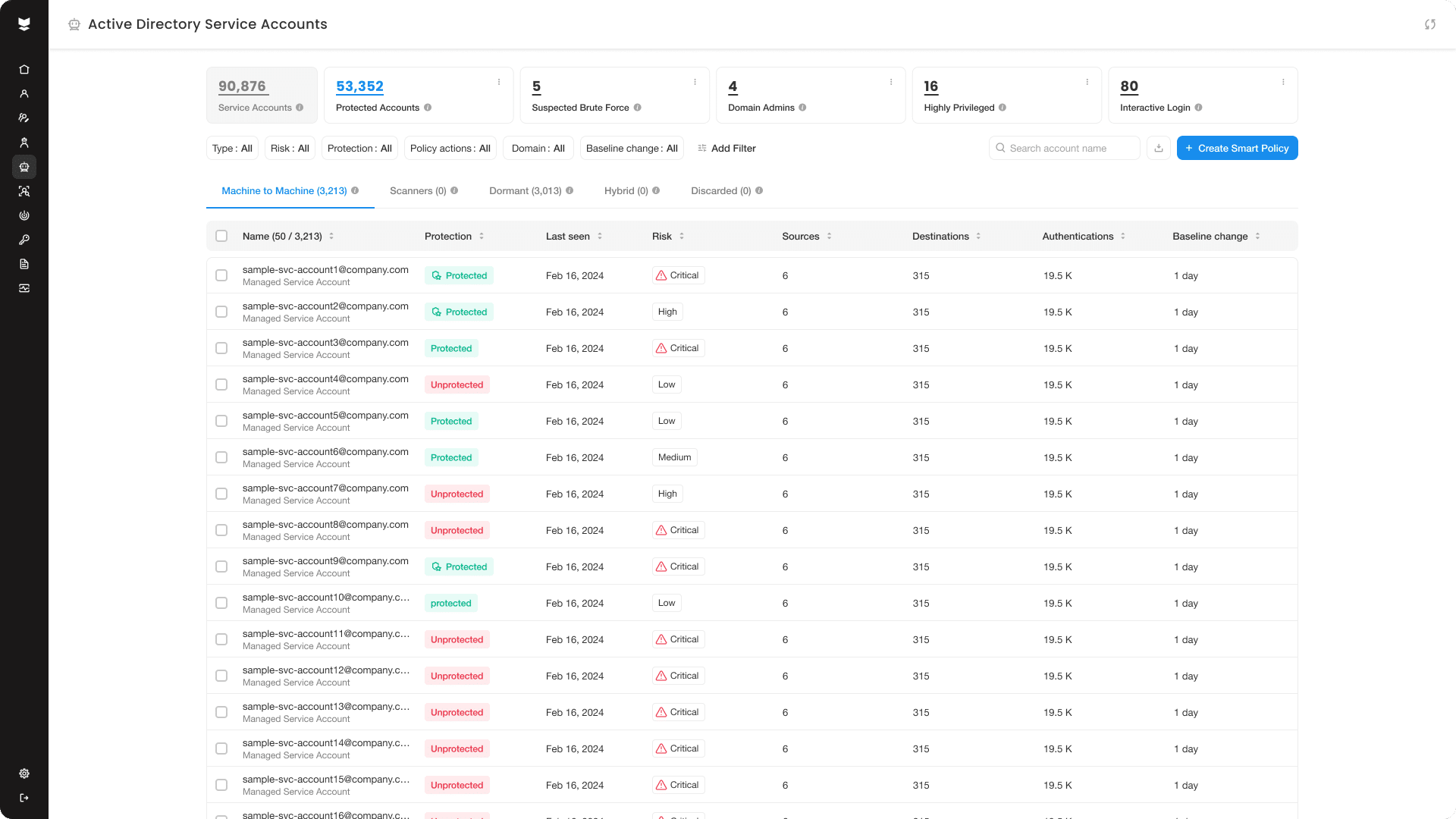
Easily discover, classify, and secure your AD service accounts. Gain full visibility into their activities and enforce virtual fencing policies to secure them against compromise.
No longer a blind spot.
Overcome all the traditional difficulties of service account protection and make what was once a painstaking manual effort into an easy, automated task.
Visibility into all accounts
Automate the discovery of each and every service account in your environment, its type, privilege level, and security posture.
Activity mapping
Drill down to find your service accounts’ sources and destinations to discover the processes they support and any application dependencies.
Protection at scale
Apply auto-generated policies to protect multiple accounts in a single click, confining them to their designated destinations and blocking any access outside this scope.
The Silverfort Identity Security Platform
How it works

From visibility to protection,
the whole journey made easy.
Discover and classify
See all your service accounts with zero manual effort. Get deep insights into their activity patterns, types and any potential misuse, as well as their the activity patterns and indicators of potential risk.
Map and prioritize
Single out the accounts that matter most based on their access privilege access, target services, and other parameters of choice, so your critical accounts are first in line to be protected.
Protect and scale
Group accounts of your choice under a smart policy that can detect when each of them deviates from its access baseline and either alerts or block its access. Add more accounts to this policy as you gradually progress in coverage.

We dared to push identity security further.
Discover what’s possible.
Set up a demo to see the Silverfort Identity Security Platform in action.


