By Dana Tamir, VP Market Strategy, Silverfort
May 2nd, 2019 is national password day – a good opportunity to discuss our ‘love-hate’ relationship with passwords. There are many reasons why we can’t rely on password-only authentication mechanisms. Yet we can’t really get rid of them either. Let me explain:
The Problem with Passwords
When users are asked to create passwords – whether they are opening new accounts or changing passwords of existing accounts – they are likely to choose passwords they can remember. The problem is that many users choose weak passwords, that can be easily guessed. A recently published list of the most commonly used passwords in 2018 shows a grim picture. It claims the most commonly used password is ‘123456’, and the 2nd spot is the obvious choice, ‘password’.
True, some people use stronger passwords. However, many reuse the same password across multiple systems and websites. Research shows that 52% reuse the same password for multiple, but not all, accounts, while another 13% reuse the same password for all of their accounts. Some even use the same passwords across both work-related systems and personal applications. This makes a stolen or compromised user password more valuable than ever.
And, if you think that requiring users to regularly change their passwords can help, well, I’m sorry to tell you it doesn’t. That’s because those who do regularly change their passwords, too often make only small and predictable changes to their existing passwords. One reason for this weakness might well be their emotional connection to their password selection routine.
This is the reason behind Microsoft’s recent announcement that it will be dropping the password expiration policies: “Periodic password expiration is an ancient and obsolete mitigation of very low value, and we don’t believe it’s worthwhile for our baseline to enforce any specific value. By removing it from our baseline rather than recommending a particular value or no expiration, organizations can choose whatever best suits their perceived needs without contradicting our guidance” explains Aaron Margosis.
No wonder that brute-force attacks, which use a trial-and-error method to obtain a user’s password, and phishing scams, which fraudulently attempt to obtain user’s passwords by disguising as communications from trusted people or organizations, are on the rise.
Data Breaches Involving Compromised Credentials On The Rise
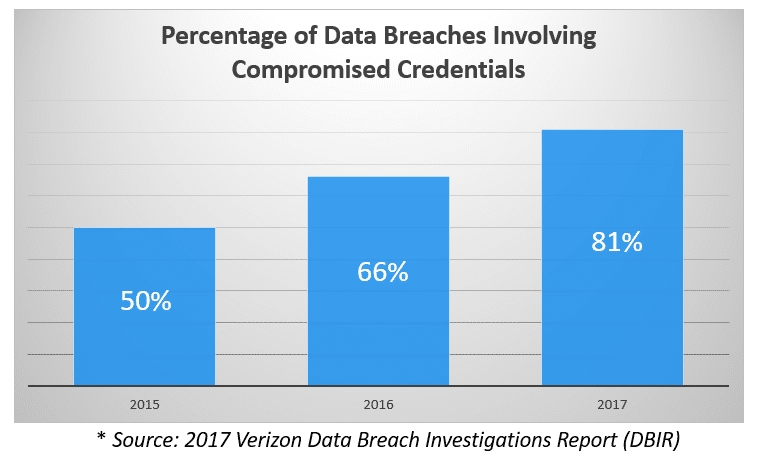
Considering everything we’ve discussed so far, it’s not surprising that compromised credentials are leveraged in more and more breaches. In fact, 4 out of 5 breaches today involved the use of compromised credentials. The problem is that when passwords or their corresponding hashes are stolen, it’s difficult to detect or restrict their unauthorized use. Or is it?
Why Can’t We Live Without Them?
Why can’t we get rid of passwords? Surely someone can come up with a better solution to authenticate users? Yes, that’s true – there are better ways to authenticate users and validate their identities. However, passwords aren’t going away anytime soon. You see, our corporate networks are built on password-based authentication protocols, and these protocols will stay with us for many years. Many of our homegrown and legacy systems are designed for password-only authentication. Modifying our network protocols and changing the authentication methods of existing systems and servers just to avoid passwords isn’t practical. So no, passwords aren’t going away any time soon.
If You Can’t Get Rid of Passwords – Add Another Layer To Them
The reality is that password-only authentication mechanisms aren’t secure enough. So what can be done to make authentication processes more secure? The answer has been known for a while: layer them with an additional authentication mechanism.
Multi-Factor Authentication (MFA) solutions, sometimes referred to 2FA, have been available for decades. They provide that additional authentication layer by requiring users to authenticate with an additional factor before they are granted access to sensitive systems. Over the years they have been proven as an effective and critical security measure to prevent the exploitation of stolen/compromised credentials.
So Why Aren’t We Using Them To Protect All Of Our Sensitive Systems?
While many organizations are looking to protect many proprietary, homegrown and legacy systems with MFA, they find it very difficult to do. That’s because mainstream MFA solutions require either the implementation of software agents on each protected system, or implementation of proxies, or local configurations and integrations. These requirement make it difficult and sometimes impossible to deploy them on these types of systems.
How Can Silverfort Help?
Silverfort offers the first agentless, proxy-less, authentication platform seamlessly enabling MFA for any sensitive system, including those that couldn’t be protected until today. These include: proprietary, homegrown and legacy systems, critical IT infrastructure, file shares and databases, IoT devices, SCADA servers, medical systems like PACS and EHR, and many more.
If you want to learn more, please contact us.
Final Note:
As I wrote this blog, I was reminded of a brilliant campaign that launched a few years ago (don’t know the source):

Treat your passwords like your underwear:
- Never share them with anyone
- Change them regularly
- Keep them off your desk
I’d like to suggest a 4th recommendation:
- Put something over them…
Dana Tamir, VP Market Strategy, Silverfort
Dana is a veteran of the cybersecurity industry with over 15 years of real-world expertise and leadership roles in leading security companies. Prior to Silverfort, Dana served as VP Marketing at Indegy. Before that, she served as Director of Enterprise Security at Trusteer (acquired by IBM in 2012). She also held various roles at Imperva, Symantec, Bindview, and Amdocs. Dana holds an engineering degree from the Technion – Israel Institute of Technology, in addition to a number of industry and vendor certifications.
To learn more about Silverfort and see a demo, contact us today!
Wishing everyone a Happy National Password Day!


