In recent years, the healthcare industry has witnessed a notable surge in consolidation, with numerous hospitals, clinics, and healthcare providers joining forces to form larger entities. This consolidation wave brings various benefits such as improved coordination, economies of scale, and streamlined operations. However, amid this transformation, the visibility gaps into healthcare services’ users and resources emerge as a crucial aspect that demands more attention. In this article, we’ll explain how Silverfort empowers healthcare organizations to quickly deploy their new environments while gaining complete visibility into the incoming users and resources.
The Security Risks that Healthcare Consolidation Introduce
As healthcare organizations acquire other healthcare services, they consolidate the newly acquired patient information, business operations, and IT environments. As part of this consolidation, IT teams need to merge the different technologies and resources as they become increasingly interconnected. The newly integrated environment brings different IT systems, networks, and user accounts into a unified infrastructure. This can result in a complex environment in which administrators may struggle to comprehensively understand all the resources, applications, and users in the consolidated entity.
In the typical case of healthcare organization consolidation, the new consolidated entity needs to understand how they can combine all domains, and move all resources to one unified IT infrastructure. This means understanding the type of accounts and resources you need to migrate. For example, which accounts are service accounts, and what kind of applications you need to merge. In most cases, the IT team won’t know much about the environment or the users they are receiving. This creates a major blind spot in which organizations don’t know the details of the incoming environment and what they are getting.
From a security perspective, the key challenge is the lack of complete visibility across the new environment, the different resources, and the users that come with it. This lack of proper visibility can potentially bring more security risks to their environment.
Silverfort’s Domain Consolidation Protection
Silverfort enables healthcare organizations to easily migrate new environments, and onboard resources and users to the main entity domain, which helps allows the newly merged environment to become operational faster.
In addition, by migrating all resources and users, Silverfort can enable healthcare organizations to gain better visibility into their environments, allowing them to protect not the environment that you’re acquiring, but their own environment to ensure they understand the risks involved in onboarding the new environment. By enforcing new security measures with Silverfort, organizations are becoming more proactive against incoming cyber threats such as lateral movement attacks.
Now, let’s show how you can gain visibility into all the resources and users in the Silverfort console.
Adding New Domains to Silverfort
In the Silverfort system settings, choose Silverfort Nodes. Here you will add your node connecting Silverfort to the virtual machine you put in the new environment. This will allow Silverfort to gather information about the new environment’s resources, users, and insights.
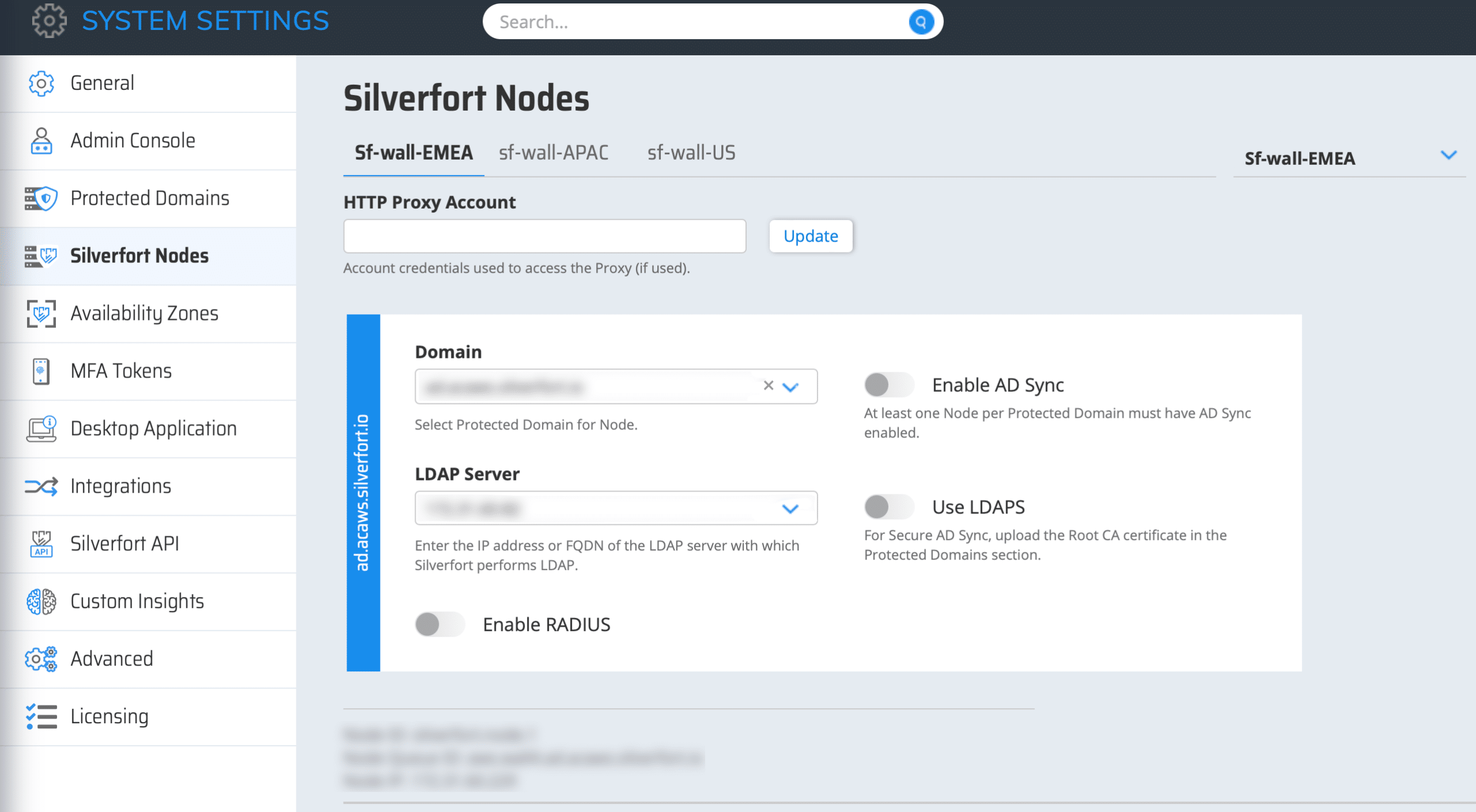
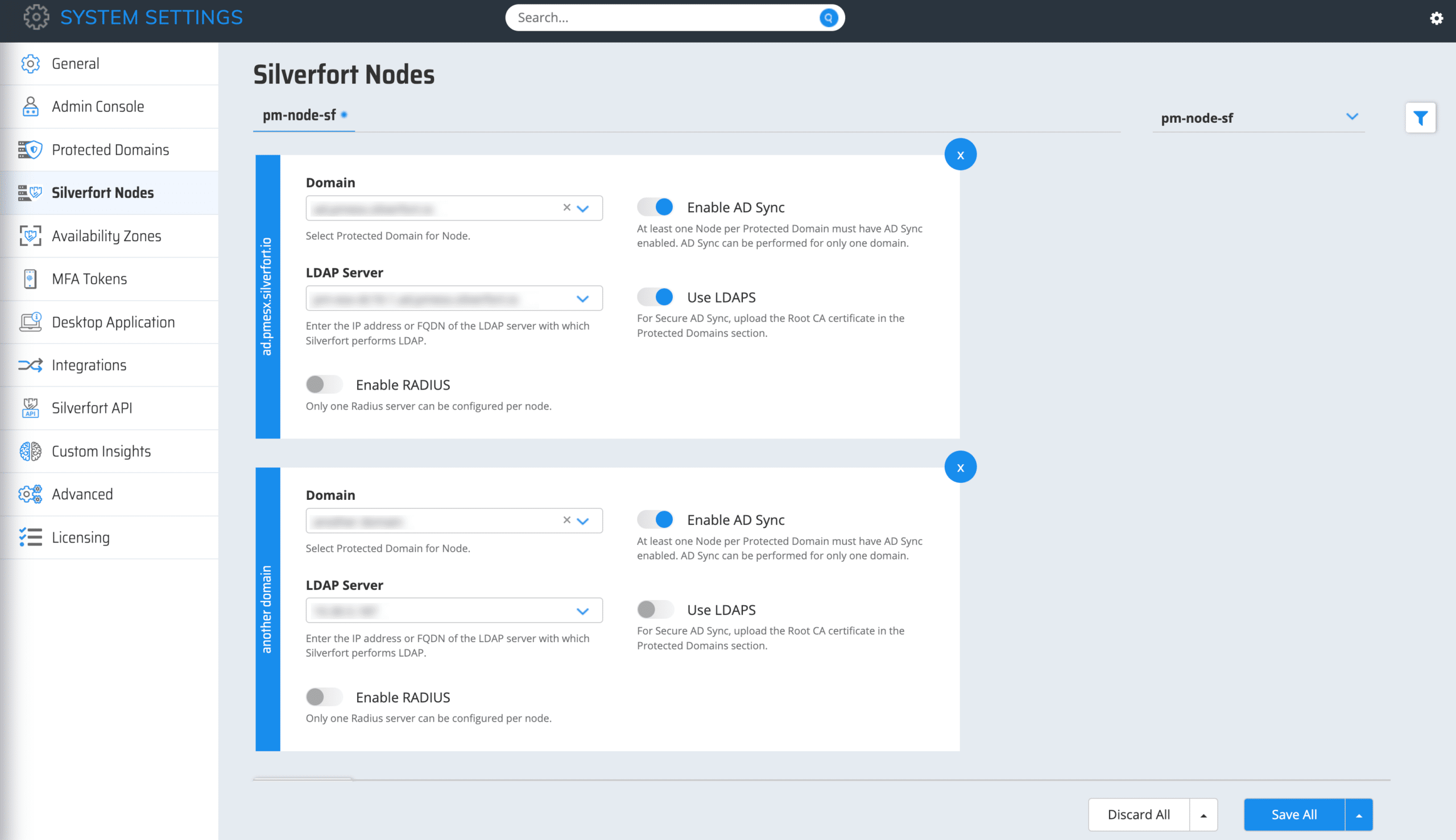
Multi-Domain Support
Recently, we added a multi-domain support capability. This allows organizations to use one node for all their domain environments. A single node will provide Silverfort with all the information about each environment.
Visibility and Monitoring of Service Accounts
Silverfort automatically identifies Service Accounts in your environment. This is because, as machine accounts, service accounts display predictable behavior patterns, allowing Silverfort to identify and categorize them automatically In the Service Accounts screen, these accounts are shown. Silverfort categorizes all detected service accounts into three main types: Machine to Machine (M2M) Accounts, Hybrid Accounts, and Scanners.
Once all the migrated service accounts are detected, you can monitor service account activity and associated risks. Silverfort provides real-time insights and visibility into all service account details and behavior, and constantly monitors and audits their use.
By continuously monitoring all authentication and access activity of the migrated service accounts, Silverfort can assess the risk of every authentication attempt and detect any suspicious behaviors or anomalies.
Next, the final step of consolidating environments is full visibility into user authentication activity.
Visibility of User Activity & Authentications
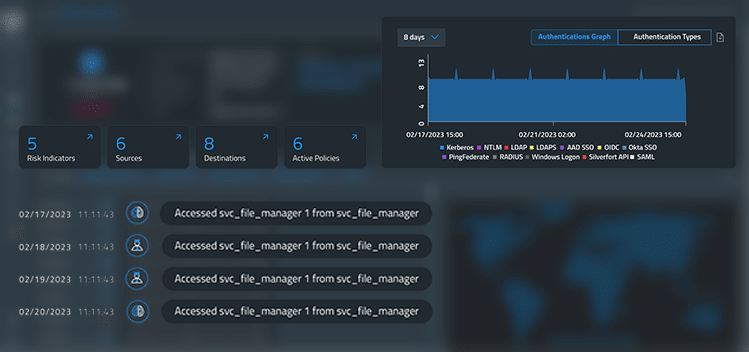
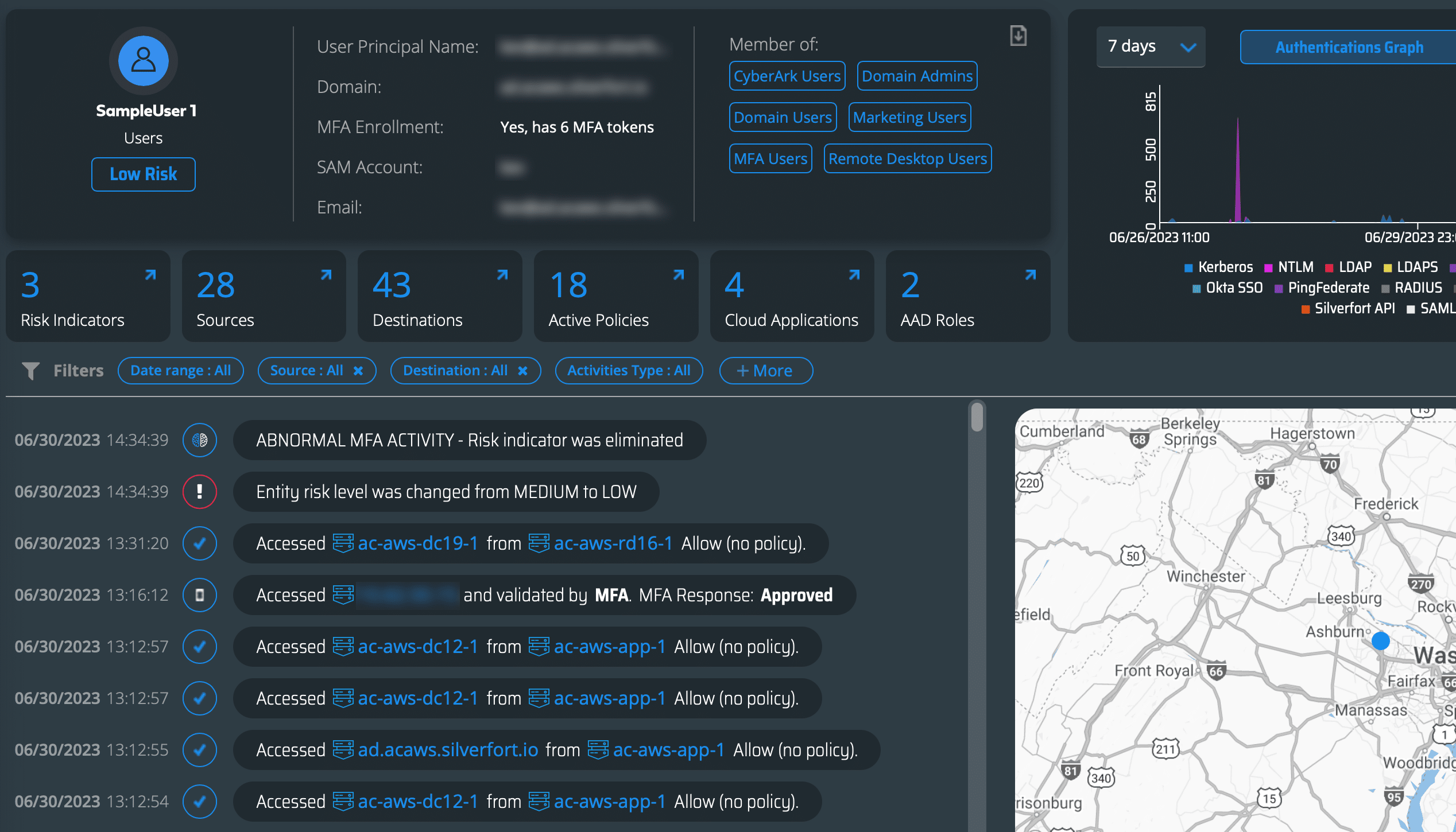
In the Logs screen in the Silverfort console, organizations will have complete visibility into all their user logs and authentication activity. From the consolidation perspective, in this screen, organizations will understand who all the incoming users are, what they are trying to access, and what their risk score is.
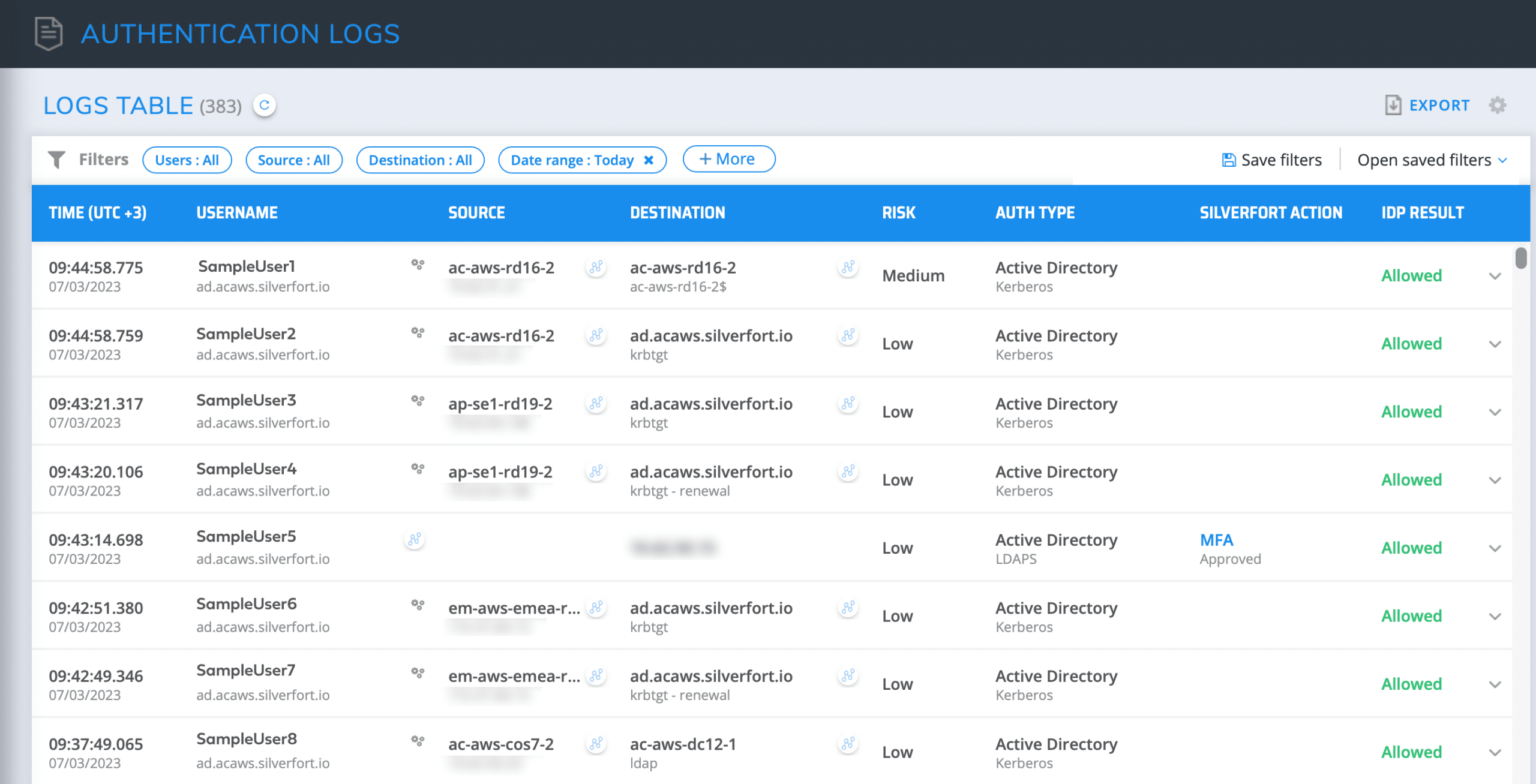
By clicking on the investigate icon next to a user in the Logs screen, you can see details of the user’s logs, authentication activity, risk indicators, and more actionable insights about the user’s activity. With these details of the user’s activities, organizations are equipped with all the information needed to have complete visibility into each user and their authentication activity.
With complete visibility into the migrated resources, service accounts, and users, healthcare organizations can sleep at night knowing that they have a complete picture of their consolidated environment.
Real-Time Visibility is the Answer for a Secure Consolidated Environment
Silverfort’s capabilities to increase the visibility into all resources and users in consolidated environments will help healthcare organizations become more operational and secure within a few days after migrating the newly acquired environment.
The consolidation of environments’ main goal is about simplifying and optimizing all their resources and users into one environment. By implementing this approach, a key complement is having complete visibility across the environment. By applying continuous monitoring and risk analysis with every migrated resource, service account, and user, Silverfort empowers healthcare organizations to be equipped with detailed insights into every authentication and access attempt while providing real-time protection for their entire consolidated environment.